Authenticated Persistent XSS Vulnerability in Shortcode For Current Date
The WordPress plugin Shortcode For Current Date, which has 10,000+ installations according to wordpress.org, is currently closed on the WordPress Plugin Directory with this message:
This plugin has been closed as of July 5, 2021 and is not available for download. This closure is temporary, pending a full review.
The changelog for the version released earlier today is:
Security issue fix.
Our monitoring alerted us to that new version, due to the mention of a security fix, and we then went to check if we should warn customers of our service using that plugin about a vulnerability that had been fixed.
The changes made in that version, though, don’t appear to include any security fix. Or any substantive change that we might have missed being a security fix.
Update: It appears the security fix might refer to changing the URL for the plugin, as the old one redirects to a strange address.
Based on what the plugin does, there was an obvious security issue to check for and through that we found the current version of the plugin contains an authenticated persistent cross-site scripting (XSS) vulnerability.
Shortcode Attribute Security
As the plugin’s name suggests, it has a shortcode. Using that shortcode calls the function sfcd_date_shortcode():
38 | add_shortcode( 'current_date', array( $this, 'sfcd_date_shortcode' ) ); |
A common security issue with shortcodes is that attributes of those, which are user input, are not properly secured using some combination of validation, sanitization, and escaping. That is the case with this plugin, as both the size and color attributes are output without any of those happening:
47 48 49 50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 | public function sfcd_date_shortcode( $atts ) { /** * Shortcode attributes. * * @since 1.0 */ $atts = shortcode_atts( array( 'format' => '', 'size' => '', 'color' => '' ), $atts ); if ( !empty( $atts['format'] ) ) { $dateFormat = $atts['format']; } else { $dateFormat = 'jS F Y'; } /* Changed [return date( $dateFormat );] * to the following line in order to retrieve * WP time as opposed to server time. * * @author UN_Rick */ if ( !empty( $atts['size'] ) || !empty( $atts['color'] ) ) { if ( $dateFormat == 'z' ) { return "<p class='sfcd-date' style='font-size:" . $atts['size'] . "; color: " . $atts['color'] . ";'>" . ( date_i18n( $dateFormat ) + 1 ) . "</p>"; } else { return "<p class='sfcd-date' style='font-size:" . $atts['size'] . "; color: " . $atts['color'] . ";'>" . date_i18n( $dateFormat ) . "</p>"; } |
That allows for XSS to occur, though by default, high level WordPress users are allowed to do the equivalent of that as they have the unfiltered_html capability. But as the proof of concept below confirms, a user with the Author, which doesn’t have that capability, can exploit this.
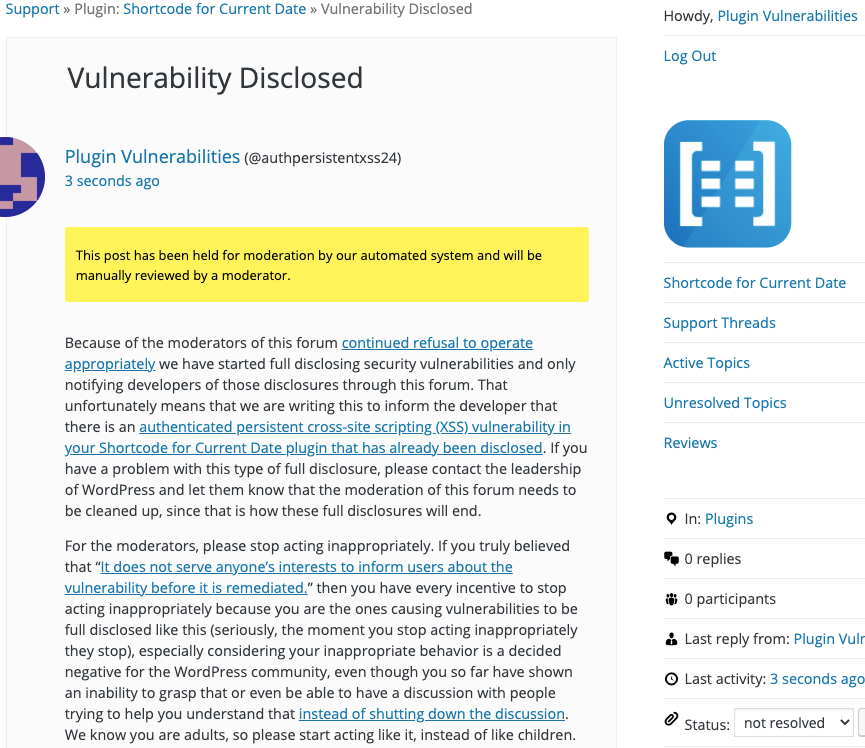
WordPress Causes Full Disclosure
Because of the moderators of the WordPress Support Forum’s continued inappropriate behavior we changed from reasonably disclosing to full disclosing vulnerabilities for plugins in the WordPress Plugin Directory in protest, until WordPress gets that situation cleaned up, so we are releasing this post and then leaving a message about that for the developer through the WordPress Support Forum. (For plugins that are also in the ClassicPress Plugin Directory, we will follow our reasonable disclosure policy.) You can notify the developer of this issue on the forum as well. Hopefully, the moderators will finally see the light and clean up their act soon, so these full disclosures will no longer be needed (we hope they end soon). You would think they would have already done that, but considering that they believe that having plugins, which have millions installs, remain in the Plugin Directory despite them knowing they are vulnerable is “appropriate action”, something is very amiss with them (which is even more reason the moderation needs to be cleaned up).
Update: To clear up the confusion where developers claim we hadn’t tried to notify them through the Support Forum (while at the same time moderators are complaining about us doing just that), here is the message we left for this vulnerability:
Is It Fixed?
If you are reading this post down the road the best way to find out if this vulnerability or other WordPress plugin vulnerabilities in plugins you use have been fixed is to sign up for our service, since what we uniquely do when it comes to that type of data is to test to see if vulnerabilities have really been fixed. Relying on the developer’s information can lead you astray, as we often find that they believe they have fixed vulnerabilities, but have failed to do that.
Proof of Concept
Creating a new post as a user with the Author role, which doesn’t have the unfiltered_html, with the following shortcode will cause an alert box with any available cookies to be shown when hovering over the plugin’s content on the page.
[current_date format="F, Y" size="' onmouseover='alert(document.cookie);"]