Privilege Escalation Vulnerability in Razorpay for WooCommerce
Yesterday, the WordPress plugin Razorpay for WooCommerce was closed on the WordPress Plugin Directory. Because that is one of the 1,000 most popular plugins in that directory (it has 70,000+ installs), our systems warned us about the closure and we started checking over the plugin to see if there was a vulnerability we should warn customers of our services about. What we found was that it contains what appears to be a very serious vulnerability.
The plugin registers four functions to be accessible through an admin post request by anyone logged in to WordPress:
10 11 12 13 | add_action('admin_post_rzp_direct_transfer', 'razorpayDirectTransfer'); add_action('admin_post_rzp_reverse_transfer', 'razorpayReverseTransfer'); add_action('admin_post_rzp_settlement_change', 'razorpaySettlementUpdate'); add_action('admin_post_rzp_payment_transfer', 'razorpayPaymentTransfer'); |
Those appear to only be intended to be accessed by Administrators, based on the pages they look to be intended to be called from. As well as the names of the functions.
Looking at the first one, razorpayDirectTransfer(), though, there isn’t a check to make sure only Administrators are accessing that:
1231 1232 1233 1234 1235 | function razorpayDirectTransfer() { $routeAction = new RZP_Route_Action(); $routeAction->directTransfer(); |
18 19 20 21 22 23 24 25 26 27 28 29 30 31 32 | function directTransfer() { $trfAccount = sanitize_text_field($_POST['drct_trf_account']); $trfAmount = sanitize_text_field($_POST['drct_trf_amount']); $pageUrl = admin_url('admin.php?page=razorpayRouteWoocommerce'); try { $transferData = array( 'account' => $trfAccount, 'amount' => (int)round($trfAmount * 100), 'currency' => 'INR' ); $this->api->transfer->create($transferData); |
So it looks like anyone logged in to WordPress can take several payment actions they shouldn’t be able to. We didn’t test this, since it would involve connecting to the payment service the plugin is tied to.
There is also a lack of a nonce check to prevent cross-site request forgery (CSRF), so the issue could be exploited that way to.
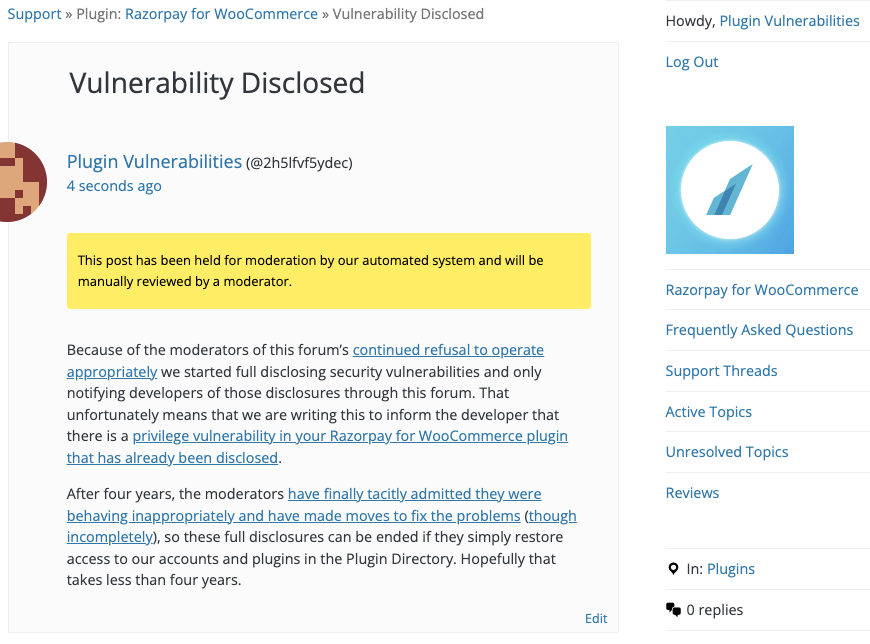
WordPress Causes Full Disclosure
As a protest of the moderators of the WordPress Support Forum’s continued inappropriate behavior we changed from reasonably disclosing to full disclosing vulnerabilities for plugins in the WordPress Plugin Directory in protest, until WordPress gets that situation cleaned up, so we are releasing this post and then leaving a message about that for the developer through the WordPress Support Forum. (For plugins that are also in the ClassicPress Plugin Directory, we will follow our reasonable disclosure policy.)
You can notify the developer of this issue on the forum as well.
After four years, the moderators have finally tacitly admitted they were behaving inappropriately and have made moves to fix the problems (though incompletely), so these full disclosures can be ended if they simply restore access to our accounts and plugins in the Plugin Directory. Hopefully that takes less than four years.
Update: To clear up the confusion where developers claim we hadn’t tried to notify them through the Support Forum (while at the same time moderators are complaining about us doing just that), here is the message we left for this vulnerability: