Cross-Site Request Forgery (CSRF) Vulnerability in Clearfy
While trying to work through a vulnerability claim with a non-working proof of concept that a vulnerability had previously existed in the WordPress plugin Clearfy, we noticed a minor but rather obvious vulnerability in the plugin. That involves a lack of protection against cross-site request forgery (CSRF) when accessing one of it options for cache clearing. An attacker could cause an Administrator to clear the cache without intending it, which shouldn’t be much of an issue, unless it could be combined with another more serious issue.
The plugin has an admin bar item. It includes two cache clearing options. The URL for one of those, “Clear all cache”, looks like this: /wp-admin/plugins.php?wclearfy_cache_delete=1. The URL for the other one of those, “Clear cache (0%)”, looks like this: /wp-admin/plugins.php?wbcr_mac_clear_cache=1&_wpnonce=11522b67fc. The second URL format includes a nonce, which is used to prevent CSRF.
The underlying code that handles the first link, which is located in the file /components/cache/includes/cache.php, is as follows:
11 12 13 | add_action('init', function () { if( current_user_can('manage_options') && isset($_GET['wclearfy_cache_delete']) ) { WCL_Cache_Helpers::deleteCache(); |
That code will run when a WordPress page loads and allows anyone with the manage_options capability, so Administrators, to delete cache. Unsurprisingly, based on the URL there is a missing nonce check to prevent CSRF.
We also found another location with code that looks similarly insecure, the function save_cdn_integration() in the file /components/cache/includes/todo_cdn.php. It looks like that isn’t accessible. Based on the name of the file it is in, it is possibly development code, which, if true, seems like it shouldn’t be in a production release of the plugin.
WordPress Causes Full Disclosure
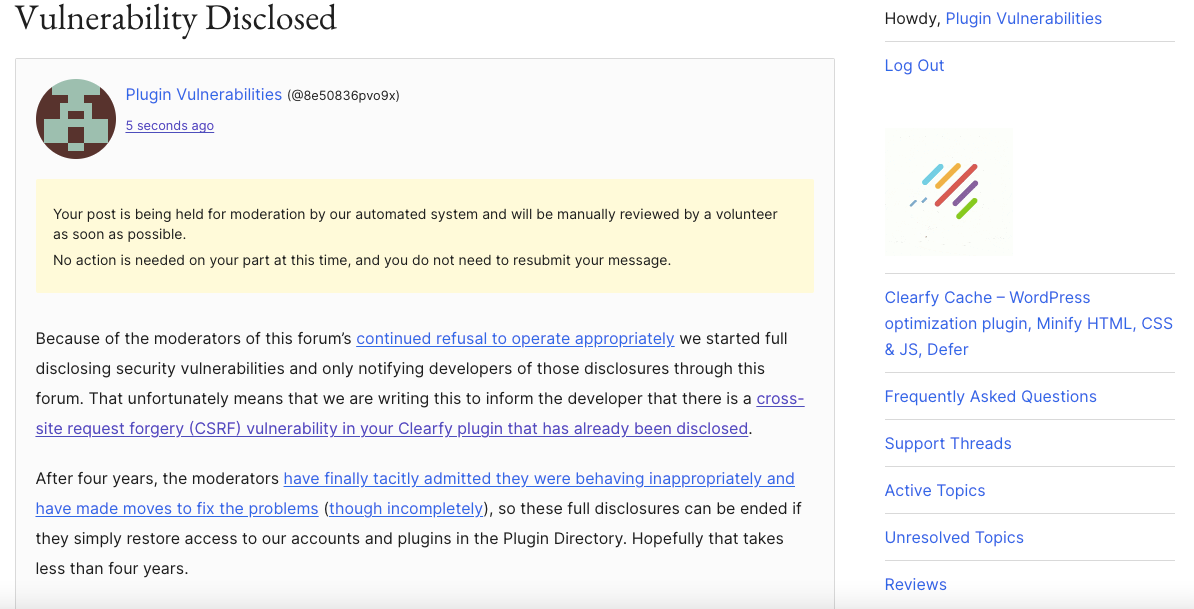
As a protest of the moderators of the WordPress Support Forum’s continued inappropriate behavior we changed from reasonably disclosing to full disclosing vulnerabilities for plugins in the WordPress Plugin Directory in protest, until WordPress gets that situation cleaned up, so we are releasing this post and then leaving a message about that for the developer through the WordPress Support Forum. (For plugins that are also in the ClassicPress Plugin Directory, we will follow our reasonable disclosure policy.)
You can notify the developer of this issue on the forum as well.
After four years, the moderators have finally tacitly admitted they were behaving inappropriately and have made moves to fix the problems (though incompletely), so these full disclosures can be ended if they simply restore access to our accounts and plugins in the Plugin Directory. Hopefully that takes less than four years.
Update: To clear up the confusion where developers claim we hadn’t tried to notify them through the Support Forum (while at the same time moderators are complaining about us doing just that), here is the message we left for this vulnerability:
Is It Fixed?
If you are reading this post down the road the best way to find out if this vulnerability or other WordPress plugin vulnerabilities in plugins you use have been fixed is to sign up for our service, since what we uniquely do when it comes to that type of data is to test to see if vulnerabilities have really been fixed. Relying on the developer’s information can lead you astray, as we often find that they believe they have fixed vulnerabilities, but have failed to do that.
Proof of Concept
The following proof of concept will purge the plugin’s cache, when logged in to WordPress as an Administrator.
Make sure to replace “[path to WordPress]” with the location of WordPress.
http://localhost/[path to WordPress]/wp-admin/plugins.php?wclearfy_cache_delete=1