Ridiculous Vulnerability Report: NextGEN Gallery Cross site Scripting (XSS) Vulnerability
All too often we see that very serious security issues are not treated with the significance they should. What doesn’t help that situation is when security companies and other in the security community take relatively minor issues and try to make them in to something much larger than they actually are. Let’s take a look at an example that we came across the other day while reviewing new reports of vulnerabilities in WordPress plugins.
A company named Cyber Security Works put out a report claiming there is a “High” risk cross-site scripting vulnerability in the NextGEN Gallery plugin. The vulnerability report describes it as such:
Cross Site Scripting (XSS) vulnerability in WordPress plugin Gravity Forms. By exploiting a Cross-site scripting vulnerability the attacker can hijack a logged in user’s session by stealing cookies. This means that the malicious hacker can change the logged in user’s password and invalidate the session of the victim while the hacker maintains access.
That sounds serious, but near the end of the report it becomes clear that it is not a serious issue at all:
Users: You MUST be an Administrator and logged into the site as an Administrator in order to enter/test XSS html testing code in the reported variables. Please do NOT actually try this test. It has been updated for security awareness
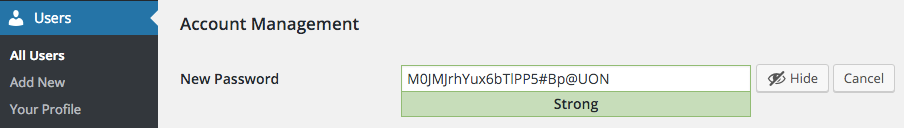
If a “malicious hacker” has access to an Administrator level account you have much bigger problems than the potential of the being able to exploit a cross-site scripting (XSS) vulnerability in a plugin, since that user would usually have almost unlimited access to the website. For example, they don’t need to exploit a vulnerability in a plugin to change someone’s password they can just do that from the Edit User page:
They would normally be able to modify plugins with that level of access as well, so the relative security of a plugin is of little importance at that point since the hacker could just change the plugin in any way they wanted.
The other issue with this is that Administrator level users (as well as the lower level Editor users) are specifically given the capability to use unfiltered HTML, so even without any plugins even installed they can do the equivalent of cross-site scripting and therefore in most cases what Cyber Security Works is labeling as a vulnerability is not that. The only time this could be considered a vulnerability is if the unfiltered HTML capability was disabled on a website, which it almost never is.