Arbitrary Directory Download Vulnerability in Download Plugin
In looking at security vulnerabilities we have found that any WordPress plugin could have a serious vulnerability, like the authenticated option deletion vulnerability we found in two related plugins for adding social media buttons that would have allowed any logged in user to disable a website, but certain plugins present more obvious risks. Despite the obvious risks, that doesn’t mean that anyone is actually doing any checking on them. A recent pair of vulnerabilities we found is an example of that.
One type of vulnerability that we see hacker frequently trying to exploit through WordPress plugins is what we refer to as an arbitrary file viewing vulnerability, which is a vulnerability that allows the viewing of the contents of a file. That can manifest itself as the content of the files being displayed as a web page or being served up as download. Hackers try to exploit this type of vulnerability to view the contents of WordPress’s configuration file, wp-config.php, which contains the database credentials for the website.
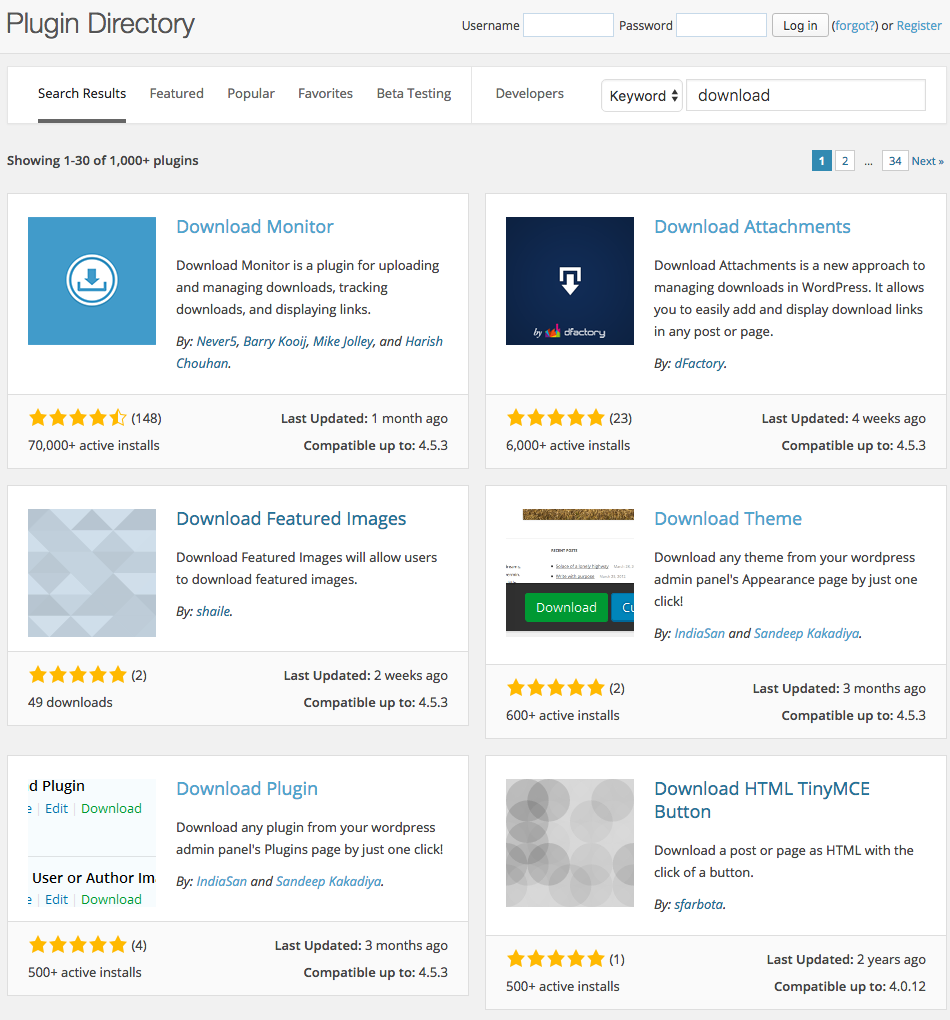
We recently went to see if we could find any WordPress plugins that involve downloading that contained such a vulnerability in them and in reminder of the poor state of the security of WordPress plugins, the first plugin we looked at had just such an issue. When we did a search for “download” on the Plugin Directory the fifth result was Download Plugin (the related Download Theme was the fourth result):
The plugin allows the contents of a plugin’s directory on the website to be downloaded.
A quick look at the plugin’s source code should that the plugin’s download functionality was available to anyone, even if they are not logged in to WordPress. The download function is set to run during the “admin_init” portion of loading an admin page:
251 | add_action( 'admin_init', 'dpwap_download' ); |
As we found recently when looking for what vulnerability hackers were likely already exploiting in another plugin, we found that when accessing the page /wp-admin/admin-post.php actions running during “admin_init” will occur even if not logged in. So when using that you need to make sure to include checks to make sure the request is being done by someone who should have access (and in some cases if they intended to do it). In this case that wasn’t happening, the only check before getting into the meat of the function is that several GET variables exist:
179 180 181 | function dpwap_download(){ if( isset( $_GET['dpwap_download'] ) && !empty( $_GET['dpwap_download'] ) && isset( $_GET['f'] ) && !empty( $_GET['f'] ) ){ |
With that access anyone could download plugins on the website, which in a lot of cases wouldn’t be that big deal if they are come directly from the Plugin Directory and the plugin’s don’t store any sensitive information in the plugin’s directory (which they usually wouldn’t, since all of the files are deleted when updating the plugin through WordPress). The plugin doesn’t limit you using directory traversal, so it is easy to instead download the root directory of the WordPress install, which gets you the wp-config.php file, as well all of the other files on the website.
The same issue impacts the Download Themes plugin as well.
Proof of Concept
The following proof of concept will ZIP up the website’s files and prompt you to download the resulting file.
Make sure to replace “[path to WordPress]” with the location of WordPress.
http://[path to WordPress]/wp-admin/admin-post.php?dpwap_download=../../&f=1
Timeline
- 7/7/2016 – Developer notified.
- 7/14/2016 – WordPress.org Plugin Directory notified.
- 7/14/2016 – Removed from WordPress.org Plugin Directory.
- 7/21/2016 – Version 1.0.2 released, which fixes vulnerability.