Taking a Stand Against the Continued Poor Handling of Security With WordPress
While WordPress handles security fairly well, there are plenty of problems that we have seen in the work have done that ultimately lead to this service and then in doing the work for to this service, including ones that are leading to websites being hacked that shouldn’t be and that make our work to actually get the security of plugins improved unnecessarily harder. Some of these problems are getting worse, so we have decided to stop doing work that people on the WordPress side should have been doing themselves all along until they present concretes plans to fix two of the many issues. In the short term this will leave those not using our service with worse security, but if WordPress chooses to start moving in the right direction then security can be improved from where it is now. We would then love to work with them to improve other issues, as there are lots of areas were small changes would likely lead to significant improvement.
Poor Handling of Security
One of the most glaring recent examples of the poor handling of security is a refusal so far to fix a vulnerability in WordPress that was disclosed to the security team in July 2016 and publicly disclosed a month ago. The explanation for not having fixed it in all that time is underwhelming:
“It’s a lower priority issue, but we are aware of it and it is in our queue to address,” Campbell said. He explained the unique set of conditions that would be required in order for this to be a serious vulnerability.
Even a low priority security issue shouldn’t take at least 11 months to fix.
A much longer running problem is that WordPress is refuses to warn people about plugins that have removed from the Plugin Directory that have security issues, despite some of those vulnerabilities being widely exploited even before the plugin is removed (something we are aware of because we have frequently been the ones to report those exploited vulnerabilities to the Plugin Directory). The main reason they have given for leaving the public in the dark is that it would put them at more risk, which doesn’t hold water.
One of the other reasons given by a forum moderator for that was:
The problem with this whole idea is that users start thinking about security incorrectly and that causes more problems then it thinks.
We are not sure how warning that websites are using vulnerable plugins causes thinking incorrectly about security, but there are much larger problems along those lines these days when it comes to WordPress. Much of that is due to security companies spreading false information about the security of WordPress. You might think that if that is reason enough not to warn about vulnerable plugins that are already being exploited, then it would also lead to people on the WordPress side taking a stand against such companies. That isn’t the case, instead we have seen them defending those companies or even promoting them in ways that normal users never could.
For example, there is one moderator the repeatedly has replied to comments about hacked websites with the following lines as part of their reply:
If you’re unable to clean your site(s) successfully, there are reputable organizations that can clean your sites for you. Sucuri and Wordfence are two.
While both of those companies are well known, the evidence doesn’t support them being reputable.
Just recently we found Sucuri falsely claiming that our website was hacked due to a page being titled “Hacked Website Cleanup”, which was yet another bad false positive from them, and we found them claiming one of their customers website was secure despite easy to spot malicious code that was compromising credit card information entered on it (and despite the customer telling them the comprises were happening).
For Wordfence, they really don’t seem to have a basic understanding of security, which appears to lead them to make false claims about security threats while claiming that they care more about security than people on the WordPress side. We also would not consider reputable a company that makes blanket claims that there plugin will protect websites from being hacked (which just from a technical prospective it can’t), while failing to protect against threats it should be able to.
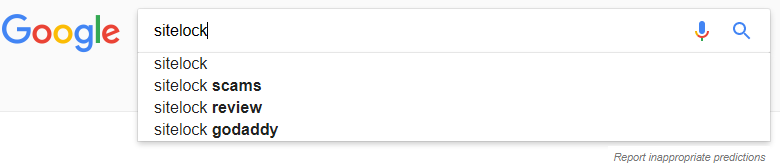
The embrace of questionable, at best, security companies, isn’t just an issue with forum moderators. When it comes to bad security companies, of which there are many, one stands out and that is SiteLock. There reputation can be summed up in what pops up as Google’s second search suggestion when you type in their name:
While there are a litany of issues we have seen with them, one that stands out if are concerned about “thinking about security incorrectly “, is their falsely claiming that WordPress websites contain vulnerabilities they don’t due to them apparently lacking even a basic understanding of how WordPress handles security (and even after it being pointed out that they were giving out bad information).
Despite that, not only is the WordPress security team giving them access to non-public sensitive security information they don’t need (the security team has time to do that, but not to fix low priority vulnerabilities) but they are allowed to sponsor and speak at various WordCamps.
Getting back to the forum moderators they have taken actions to prevent webmasters from knowing they are using vulnerable plugins while at the same time allowing unfounded security claims about plugins to remain on the forum.
We Have Stopped Notifying WordPress of Vulnerabilities in the Current Versions of Plugins
When it comes to low hanging issues with the security of WordPress plugins one of them is making sure that plugins with known vulnerabilities in the current version are not in the Plugin Directory. What we came across over five years ago was that this wasn’t happening, we tried at the time to get people on the WordPress side of things to start monitoring for that situation and taking action, but it wasn’t successful. We have at times done the monitoring for them and out of that eventually came this service. Based on the periods of time when we were not doing that for them, we are about the only ones that have, so without us reporting those the plugins often remain in the Plugin Directory indefinitely.
Seeing as this isn’t actually our responsibility to do, we feel that suspending our doing that is reasonable action to take until WordPress make concrete plans to improve two areas that impact the focus of our service and our work.
Concrete Plans Needed For Fixing Two Serious Issues
While there are a lot of areas that need fixing, we have decided that there are two areas that really are in need of fixing that directly tie in to with our service, though for one of them making the change would likely be bad for our business. Once WordPress has provided concrete plans to fix these we will start reporting the vulnerabilities to them again.
The first is there needs to be concrete plan for finally warning when plugins that have been removed from the Plugin Directory and providing at least a general reason why it was removed.
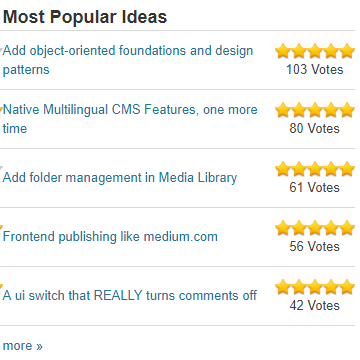
It has now been nearly five years since we suggested doing that on the Ideas section of the WordPress website and it wasn’t long after that the head of the Plugin Directory said that it was being worked on. Not only has that not happened, but the position changed that it can’t be done. Despite that the idea is still marked as “Good idea! We’re working on it”, which clearly isn’t the case. One reason that might be is that since it marked as being worked on it doesn’t getting listed on the front page of the Ideas section under Most Popular Ideas, where it otherwise would be the third most popular idea (it has 69 votes):
The continued refusal to properly handle this situation is utterly baffling to us, and from reading others comments, it seems that really isn’t something that anyone outside of the WordPress team is in agreement with them on. Their inability grasp something that is so black and white, makes trying to have a reasonable discussion about problems with their handling of security where there is more gray area seem not worth trying (we will be discussing one example of that in an upcoming post).
The second is that the moderation of the WordPress Support Forum needs a complete overhaul and likely would need a wholesale removal of the current moderators.
The problems with the forum moderation tie in with the first issue, as back in February the head of Plugin Directory, who seems to be the one spearheading leaving people in the dark about removed vulnerable plugins, shutdown a thread discussing the issue as being “non-productive”. Just based on their conflict of interest they should not have been shutting that down, but to make matters worse before they did that they allowed themselves to get the last word in thread. When you can’t even have a conversation about something that is leading to websites being unnecessarily hacked, it points to huge problem with handling security.
It was also the poor forum moderation that was the last straw with the handling of security as while we were trying to get a vulnerability fixed a moderator got in the way and falsely accused us of disclosing a vulnerability. False accusations and interrupting actual discussions are all too common from the moderators.
This issue doesn’t just impact us though. One of the things we do to keep track of vulnerabilities in WordPress plugins is monitor the Support Forum for security related threads. What we have seen is that usually the only response is from a moderator, either providing a canned response that isn’t relevant to the poster’s issue or providing incorrect information. It isn’t hard to see why that is since anyone that has actual knowledge in the area is likely to quickly run in to a moderator that doesn’t have a good grasp of security and seems to be more interested in lording over the forum then helping anyone (we wish that was hyperbole). There are plenty of posts where we could provide some insights around original poster’s issue, but it just isn’t worth the grief and false accusations that come from the moderators, we doubt we are alone in that considering that no one else is doing that.
Some of what we have seen moderators do is about as bizarre as the refusal to warn about removed plugins, as one example, one time while someone (or someones) were disappearing replies from us they deleted another person’s reply that simply thanked us. That being despite the claim that:
Forum topics will only be edited or deleted if they represent a valid legal, security, or safety concern.
What would be a legal, security, or safety concern about saying thank you?
How Does This Change Impact You
If You Already Use Our Service
For our customers we hope it doesn’t impact you much.
If you were to install a plugin that previously would have been removed due to us reporting a security issue in it, you will know get notified of the issue the next time the service’s companion plugin does a check of your installed plugins.
We already included a listing of vulnerabilities that had been in a plugin in a new tab when looking in to the details of a plugin on the “Add New” plugins page:
With the next release of the plugin we are adding a new alert on the main details page:
We looked into adding them to more broad based listing pages but that introduced some issues, which made that less than ideal, so we are not adding that at this time.
If you are using a plugin that has vulnerability in the current version we are, as we always have been, there to consult with you on what the best way of dealing with that it. It might be that you can safely ignore the vulnerability (if say it was in plugin functionality you don’t use). In most cases we can come up with a workaround until the vulnerability is properly fixed (we also try to work with developers to get the vulnerabilities in their plugins fixed). In other cases a plugin might be so insecure that the best option is just to find another plugin to use.
If You Don’t Use Our Service
You are likely going to have more issues since you are going to have an increased chance of using plugins that have security issues, including the possibility of ones that are already being exploited, as we are the only ones monitoring for that type thing, much less notifying the Plugin Directory about that. That is unless someone else takes over the monitoring and reporting that we do, but considering that never happened in time periods where we haven’t been doing that prior to starting this service, it is unlikely to happen. We will continue including vulnerabilities we see exploited in the free data that comes with companion plugin for the service, which you really should already have installed even if you are not using our service.
If you are concerned about this we would recommend you get the word out that WordPress should come up with concrete plans to fix the issues mentioned earlier in the post, so that we can go back to reporting unfixed vulnerabilities to them.
In the meantime signing up for our service will give you even better protection than you would have if we were reporting these vulnerabilities to WordPress, because while that would prevent you being able to install known vulnerable plugins, if you were already using you would still be in the dark (if they actually start warning people you would be warned without needing our service). When using our service you also have access support from a company that actual understand the vulnerabilities (other security companies don’t even understand enough to be able to check if a plugin really has a vulnerability), allow us to help developers make their plugins more secure, and the ability to suggest/vote for plugins to have security reviews done by us.


Maybe there will be a change soon. It looks like this is one of the topics to be discussed by the plugins team at the WordPress community summit: https://make.wordpress.org/summit/2017/06/10/community-summit-2017-final-list-of-topic/
Under the “Plugins” section: