Our Plugin Security Checker Identified a Reflected XSS Vulnerability in Quiz And Survey Master
Recently the plugin Quiz And Survey Master, which has 20,000+ active installs according to wordpress.org, was run through our Plugin Security Checker tool and as part of our continued focus on improving the results produced by the tool we happened to take a look at some of the possible issues identified in it. One of those possible issues was reflected cross-site scripting (XSS) vulnerability in the plugin due to user input being directly output without any escaping.
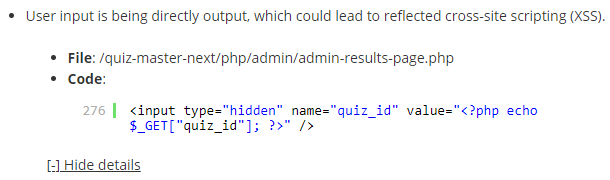
Looking at the underlying code for the identified issue, which is available to users of our service through the tool’s Developer Mode, it certainly looked like the identification was correct and that there was likely be a vulnerability due to user input being output without being escaped:
A quick check confirmed that this was an exploitable vulnerability (though far from a serious issue for the average website), as can be seen with the proof of concept below.
We notified the developer of the issue a week ago. We haven’t heard back from them and no new version has been released to fix the issue. In line with our disclosure policy, which is based on the need to provide our customers with information on vulnerabilities on a timely basis, we are now disclosing this vulnerability.
Proof of Concept
The following proof of concept will cause any available cookies to be shown in alert box when logged in WordPress as an Editor or Administrator. Major web browsers other than Firefox provide XSS filtering, so this proof of concept will not work in those web browsers.
Make sure to replace “[path to WordPress]” with the location of WordPress.
http://[path to WordPress]/wp-admin/admin.php?page=mlw_quiz_results&quiz_id="><script>alert(document.cookie);</script>
Timeline
- September 17, 2018 – Developer notified.