Outputting $_SERVER[‘PHP_SELF’] Without Escaping Isn’t Safe for WordPress Plugins
One of the frustrating aspect of dealing with the security of WordPress plugins is that so often people seem to be unwilling to learn from their mistakes. The people running the Plugin Directory, for example, seem to be creating their own reality to avoid even acknowledging their mistakes. We work hard to avoid mistakes, but when they happen we are happy to learn from them and improve what we are doing.
We recently made a mistake. In looking in to the possibility that a vulnerability had been fixed in a plugin we got things wrong and wrote this:
The changelog for the latest version of Admin renamer extended is “Changed: Possible XSS bugfix reported by CBiu”. In looking over the changes made in that version to see if this was something we should be alerting customers of our service if they were using the plugin, we found that even calling it “possible” might be overstating it.
Unrelated to that post, we were subsequently contacted by the person that had found the vulnerability, to inform us that they had disclosed a number of vulnerabilities. One of those was what had been fixed, which we missed.
The vulnerability involved the outputting of the variable $_SERVER[‘PHP_SELF’] without escaping:
113 | <form id="form1" name="form1" method="post" action="<?php echo $_SERVER['PHP_SELF'].'?page='.$_GET['page'].'&user_id='.$row->ID; ?>" > |
The PHP documentation describes that variables as follows:
The filename of the currently executing script, relative to the document root. For instance, $_SERVER[‘PHP_SELF’] in a script at the address http://example.com/foo/bar.php would be /foo/bar.php. The __FILE__ constant contains the full path and filename of the current (i.e. included) file. If PHP is running as a command-line processor this variable contains the script name since PHP 4.3.0. Previously it was not available.
As the proof of concept shows at least in the context of a WordPress plugin, you can tack on characters after the actual filename and those will be included in that variable:
http://localhost/wp-admin/plugins.php/%22%3E%3Csvg/onload=alert(/xss/)%3Ea?page=admin-renamer-extended%2Fadmin.php
After finding that out we thought that might be something that we should add to our Plugin Security Checker, which is tool to identify the possibility of some instances of security issues in WordPress plugins. To get a better idea of if this was a widespread issue and to make sure that we wouldn’t just be flagging harmless code we used the website WPdirectory to get a better idea of how common code like that is. The result was that with code that exactly matches what was in that plugin, there were 994 matches.
We then looked at one of the more popular plugins that matched that, Get Recent Comments, which has 9,000+ installs, to confirm this was something that was a problem with other plugins.
When accessing the plugin’s admin page there are multiple lines like this that run:
595 | <li><a href="<?php echo $_SERVER['PHP_SELF']; ?>?page=get-recent-comments.php&subpage=1" <?php echo $current_tab[1] ?>>Comments</a></li> |
As the proof of concept below shows, that permit reflected cross-site scripting (XSS) to occur as malicious JavaScript code from the URL could be output on the page.
The Plugin Security Checker has now been updated to flag similar code to that.
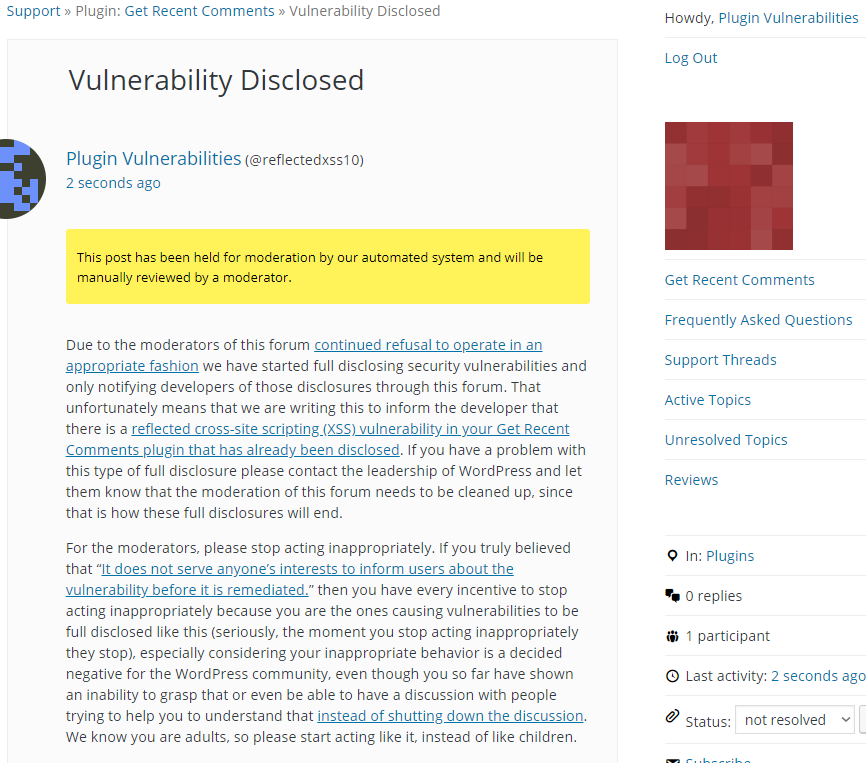
Full Disclosure
Due to the moderators of the WordPress Support Forum’s continued inappropriate behavior we are full disclosing vulnerabilities in protest until WordPress gets that situation cleaned up, so we are releasing this post and then leaving a message about that for the developer through the WordPress Support Forum. You can notify the developer of this issue on the forum as well. Hopefully the moderators will finally see the light and clean up their act soon, so these full disclosures will no longer be needed (we hope they end soon). You would think they would have already done that, but considering that they believe that having plugins, which have millions installs, remain in the Plugin Directory despite them knowing they are vulnerable is “appropriate action”, something is very amiss with them (which is even more reason the moderation needs to be cleaned up).
Update: To clear up the confusion where developers claim we hadn’t tried to notify them through the Support Forum (while at the same time moderators are complaining about us doing just that), here is the message we left for this vulnerability:
Is It Fixed?
If you are reading this post down the road the best way to find out if this vulnerability or other WordPress plugin vulnerabilities in plugins you use have been fixed is to sign up for our service, since what we uniquely do when it comes to that type of data is to test to see if vulnerabilities have really been fixed. Relying on the developer’s information, can lead you astray, as we often find that they believe they have fixed vulnerabilities, but have failed to do that.
Proof of Concept
The following proof of concept will cause any available cookies to be shown in an alert box, when logged in as an Administrator. Major web browsers other than Firefox provide XSS filtering, so this proof of concept will not work in those web browsers.
Make sure to replace “[path to WordPress]” with the location of WordPress.
http://[path to WordPress]/wp-admin/options-general.php/"><script>alert(document.cookie);</script>?page=get-recent-comments.php