Not Really a WordPress Plugin Vulnerability, Week of October 18
In reviewing reports of vulnerabilities in WordPress plugins to provide our customers with the best data on vulnerabilities in plugins they use we often find that there are reports for things that don’t appear to be vulnerabilities. For more problematic reports we release posts detailing why the vulnerability reports are false, but there have been a lot of that we haven’t felt rose to that level. In particular are items that are not outright false, just the issue is probably more accurately described as a bug. For those that don’t rise to level of getting their own post we now place them in a weekly post when we come across them.
Cross Site Scripting in FooGallery, Popup Builder, and Soliloquy
Related claimed cross site scripting vulnerabilities in the plugins FooGallery, Popup Builder, and Soliloquy involve a common cause of false reports of persistent cross-site scripting (XSS) vulnerabilities, people not understanding that WordPress allows users with the unfiltered_html capability to do the equivalent of XSS. In this case if you follow the instruction you find that you are entering the XSS code in the title of a custom WordPress post, which is permitted to happen for users with the unfiltered_html capability, but is not permitted for those without that.
In addition to that, for FooGallery and Soliloquy what is claimed to happen due to that would occur exactly the same with a regular post, so for this to be a vulnerability, WordPress would also have to be vulnerable.
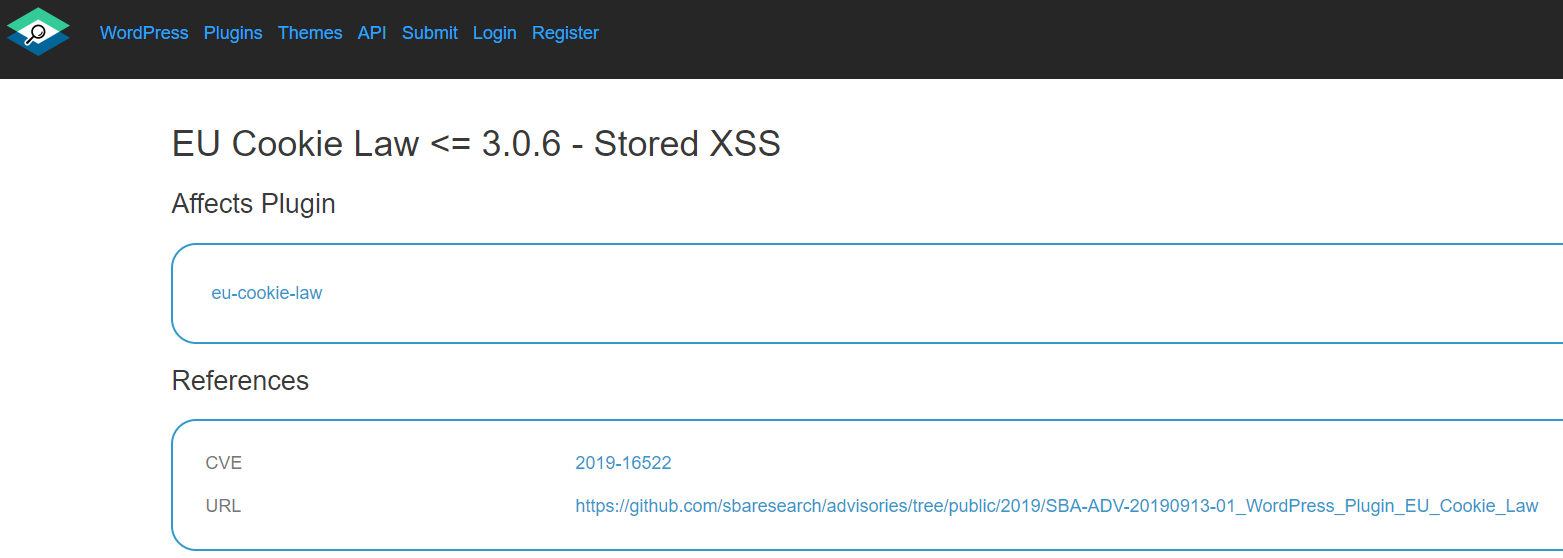
Stored XSS in EU Cookie Law
Three weeks ago in this post we noted that SBA Research had put out a false report of a vulnerability in a WordPress plugin. We had emailed them about that and replied to their tweet to try to address that with them, we have received no response. They describe themselves this way:
SBA Research was founded in 2006 as the first Austrian research center for information security by the TU Wien, the Graz University of Technology and the University of Vienna. In recent years, the Vienna University of Economics and Business, the AIT Austrian Institute of Technology and the University of Applied Sciences St. Pölten joined as academic partners.
It continues to trouble us how the lack of concern with accuracy when it comes to security involves the academic realm, which you would hope would be better than security companies.
In the meantime they have done the same thing with a claim of stored XSS vulnerability in the plugin EU Cookie Law. Like the previous instance the action they are claiming is vulnerability can only be taken by an Administrator and as we noted in the previous instance “those users are normally permitted to do the equivalent of cross-site scripting (XSS) due to having the unfiltered_html capability, they also can take other actions that would do the equivalent what could be done with this, say installing another plugin.”
As is often the case other sources will then spread claims like this, in this case that includes CVE and not at all surprisingly the WPScan Vulnerability Database: