WordPress’ Belief in Covering up Vulnerabilities in Plugins Is Disputed By Reality
In trying to improve the security surrounding WordPress plugins and therefore improve security surrounding WordPress, one of the biggest, if not the biggest, impediments is the people on the WordPress side of things. That starts with the person at the top, Matt Mullenweg, falsely claiming the only plugin security issue that isn’t “hypothetical” is people not keeping plugins updated, despite how many website have been hacked due to unfixed vulnerabilities in plugins. From there, a top impediment is that the WordPress folks have a belief that somehow hiding that publicly disclosed unfixed vulnerabilities is actually a way to keep people secure (even though if you believe the person at the top they are not even an issue). Here for example is the first paragraph on the page on how to report a plugin security issue:
If you find a plugin with a security issue, please do not post about it publicly anywhere. Even if there’s a report filed on one of the official security tracking sites, bringing more awareness to the security issue tends to increase people being hacked, and rarely speeds up the fixing.
We never have been sure what an official tracking site is (official in what way?), but it is strange argument that an issue that is already been disclosed in places where hackers are certainly already looking would be somehow be worse if it was mentioned in places where they are less likely to be looking, but where users of the plugin would be and could then take some action.
What actually should be the focus is on getting things fixed as soon as possible, something that people on the WordPress side frequently get in the way of happening, or barring that, warning people that they are using a vulnerable plugin, which they not only oppose doing, but even being able to have an open discussion of.
A case in point that hackers are going to try to exploit things even without a lot of awareness and the best option is to actually fix things, since that would actually protect people, is a hacking attempt we saw on this website over the weekend.
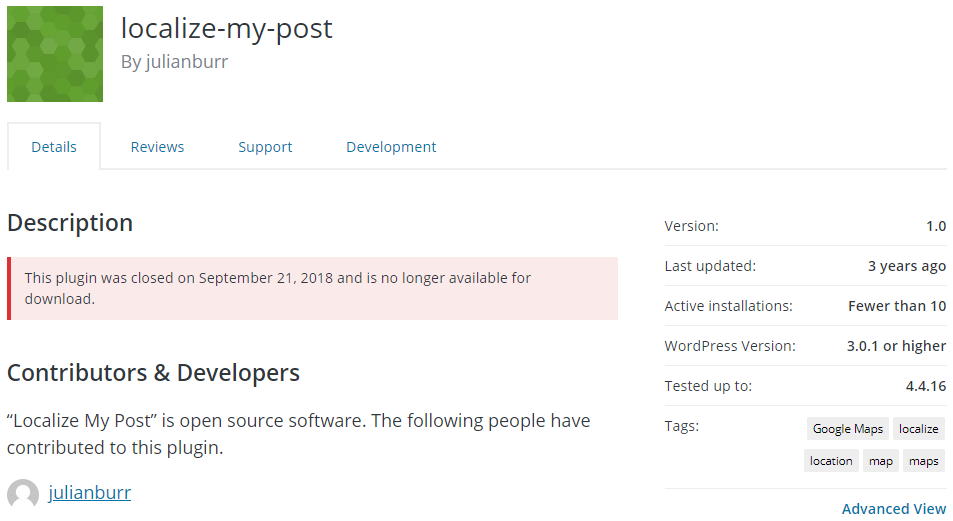
On Saturday there was a request probing for the file /wp-content/plugins/localize-my-post/ajax/include.php, which is file from the plugin Localize My Post. That file has a local file inclusion (LFI) vulnerability that was disclosed last month by Manuel Garcia Cardenas. According to wordpress.org there are less than 10 active installations of that plugin:
If the fact that almost no one uses this plugin doesn’t stop hackers from trying to exploit it, it seems highly unlikely that mentioning the WordPress Support Forum is going to have some significant impact on whether vulnerabilities are exploited. That instance is far from the first time we have seen a situation where it looks like a hacker has looked at a report of a vulnerability, but not looked at anything available on the WordPress website. In fact it was less than a week ago we mentioned another plugin being targeted by a hacker that is used on less than 10 websites and less than two weeks ago a hacker who was trying to exploit a vulnerability in way that wouldn’t work because they hadn’t actually downloaded the plugin and tested things out first.
While mentioning these vulnerabilities isn’t likely to make things worse by attracting more hackers, doing that could help to get them fixed or help people to protect themselves, which the people on the WordPress side of thing oppose for, at best, a bad reason.