Sucuri (sucuri.net) Won’t Effectively Protect Your Website
Last week we mentioned our recommendation that “if you are looking for a security product or service that will provide protection we would recommend finding one that provides evidence, preferably from independent testing, that it is effective”. That isn’t something we are aware of them providing and we have seen plenty of evidence to the contrary for many of those over the years. Take the service Sucuri as an example. Right in their marketing materials on their homepage they emphasize something that doesn’t match up with their service providing effective protection, which is that they include unlimited hack and malware cleanups:
It would be one thing if they were claiming that they are so sure of the protection they provide that they will clean up the website for free if that doesn’t work (the guarantee they mention there is really not what they make it seem to be) or if they mentioned they include hack cleanups, as many people are looking for a protection service once their website gets hacked, but they are emphasizing unlimited cleanups, when multiple cleanups shouldn’t be needed if the service is really protecting websites.
Also notably, on their homepage they tout several supposed metrics, none of which involve effective protection:
The number of cleanups, if even true, could actually be an indication of a lack of protection.
What we have seen in repeatedly being brought in to reclean up hacked websites over at our main business that they were previously hired to clean is that they don’t look to attempt to determine how the websites were hacked. That not only seems to be the source of a lot of the problems that cause us to be hired to clean up the websites again, but it is strange for a service that is supposed to be protecting websites to not be determining how they are getting hacked, since that obviously would be important to know to have a chance of protecting against them. (From what we have seen elsewhere it appears that Sucuri doesn’t have even a basic understanding of security, which might explain the lack of doing that and a lot of the other problems with them).
You don’t have to take our word on the lack of effective protection provided by this service or what Sucuri’s own marketing material would indicate, just take a look at a recent topic on the WordPress Support Forum that got flagged in the monitoring we do of that forum to keep track of info on possible security issues with WordPress plugins. The topic starts with someone describing a situation a week ago where their website was clearly not being effectively protected by Sucuri:
So Saturday Oct 13, upon logging into my site, saw an admin message from your plugin telling me to Opt in at the top of my dashboard.
Myself and my wife are the only admins.
She DOES NOT install plugins. I run the site.
Somehow this plugin was in stalled and activated.
I deactivated and deleted and immediately scanned the server and my own system. Both clean. I have sucuri.net protecting my site and scanning for malware.
A few hours later, the plugin re-appeared and reactivated.
I deleted again and called my host for tech support.
It’s been installed and activated 5x now in 2 days.
Is there ANY support you could give me to determine if this code has been altered, or if there is any sort of odd testing you’re doing that might explain this? or has anyone else said this?
WordPress seems to indicate there are less than 10 installs of this plugin out there.
There isn’t any way the plugin being mentioned there, 2MB Autocode, could have installed itself, instead someone must have had access to the website in some way to install it. That could have been directly through WordPress or by a combination of file and database access.
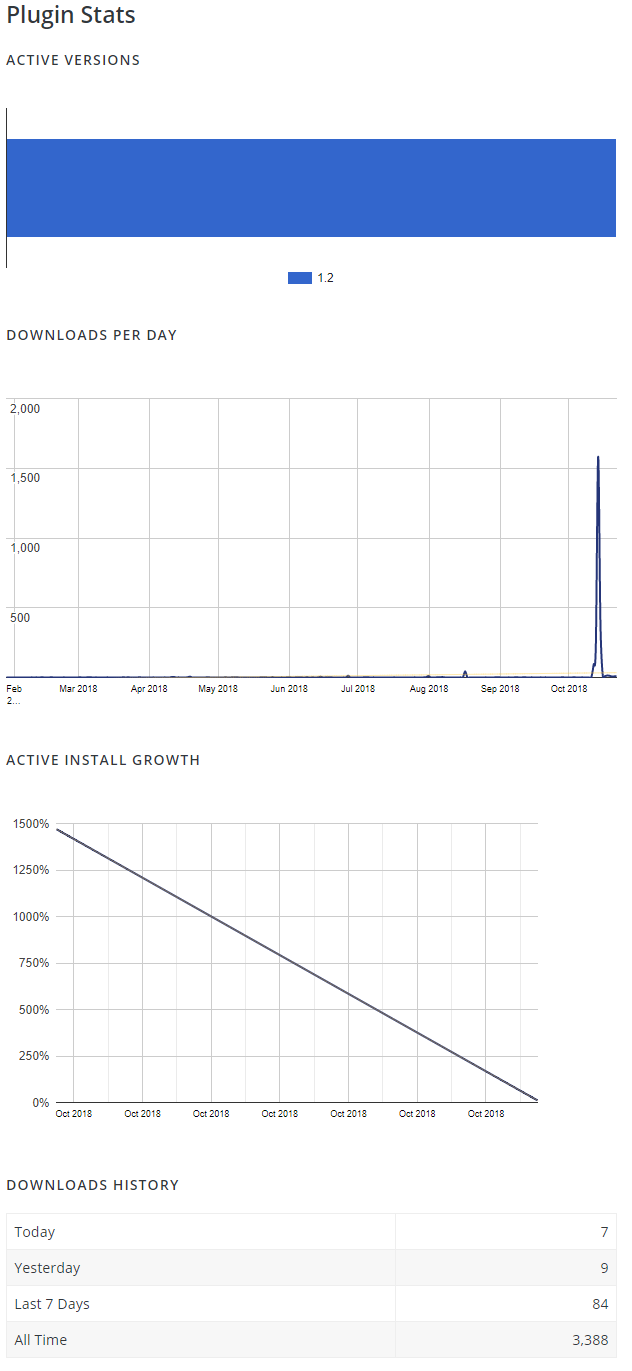
Based on the plugin’s stats, it would appear that someone was installing this on a lot of websites through WordPress last week (when installing or updating a plugin through WordPress it gets counted as a download):
At the end of the previously mentioned message it was written that “WordPress seems to indicate there are less than 10 installs of this plugin out there.”, but a week later there 200+ installations, so apparently a fair amount of those installs haven’t been removed.