The Mess that is Imperva’s Claim That WordPress Vulnerabilities Tripled in 2018
A good rule of thumb based on what we have seen over the years is that stats on security are probably not accurate. So it isn’t surprising that when we looked into a claim by a company named Imperva that WordPress vulnerabilities tripled in 2018, it was a mess, but that hasn’t stopped security journalists from repeating the claim.
When we ran across the claim our first question was what the source of their data was and looking at Imperva’s post they only give a vague explanation:
To do this, we use internal software that collects information from various data sources such as vulnerability databases, newsletters, forums, social media and more, integrates it into a single repository, and assesses each vulnerability’s priority.
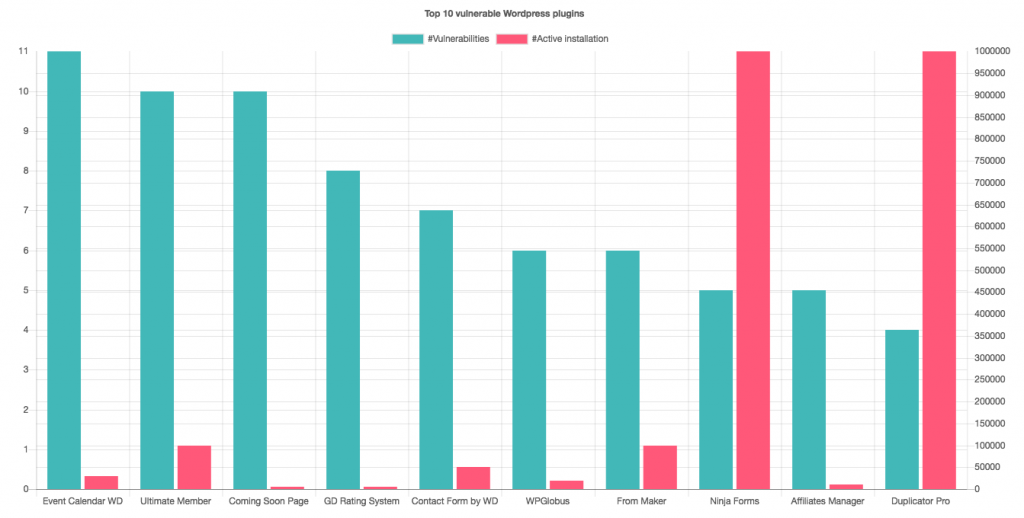
They provide this chart “Top 10 vulnerable WordPress plugins”:
Looking around various source to try to find a match or understand their sourcing we couldn’t find anywhere near 11 reports of vulnerabilities in the first plugin shown, Event Calendar WD. In fact we only found one, if you count each change made related to that vulnerability you would to more than 11, so we can’t figure out where the figure might have come from. What makes that more problematic is that the other portions of their post don’t seem to be written by someone that understands the topic at hand, so the accuracy of the data seems suspect to us.
Speaking of the problematic portions, what really makes this a mess is that this company is mixing up vulnerabilities discovered in software with other things. Right above the chart they wrote this:
In Figure 8 below, you can find the ten WordPress plugins with the most vulnerabilities discovered in 2018. Please note, that these are not necessarily the most-attacked plugins.
But at another point in their post they write this:
Despite the slowed growth in new plugins, the number of WordPress vulnerabilities tripled! The explanation for this could either be the code quality of the plugins, or the fact that WordPress is such a popular CMS, which motivate more attackers to develop dedicated attack tools and try their luck searching for holes in the code.
Since this is supposed to be measure of vulnerabilities discovered the explanation for the claimed tripling could, say, have to do with improvements in spotting vulnerabilities, not that there were more vulnerabilities. That they don’t seem to understand that raises serious questions about their whole endeavor.
What seems more important is the hypothesis that “more attackers to develop dedicated attack tools and try their luck searching for holes in the code” as that makes no sense, since the vast, vast majority of vulnerabilities being discovered are not connected to attackers. Based on what we saw during the year, the new vulnerabilities being discovered by attackers that would lead others to notice the issue (its possible that more advanced attackers are exploiting vulnerabilities that are not then spotted) would run in the tens of vulnerabilities at most (and it probably in the single digits), which is nowhere near the 542 they list as the total.
Bad Journalism
As example of example of the bad journalism based on that, take Lindsey O’Donnell at Threatpost on this. The quality of the journalism is pretty telling from this at the bottom of the post:
Automattic, the owner of WordPress, did not immediately respond to a request for comment from Threatpost.
Automattic isn’t the owner of WordPress, though you might think otherwise based on what has happened related to Gutenberg, so asking them for comment is odd.
The start of the post is also quite problematic:
Despite fewer plugins being added to WordPress last year, the CMS saw an astounding tripling of vulnerabilities in its platform in 2018.
Vulnerabilities in popular content management system (CMS) WordPress are growing at a staggering rate, almost tripling in 2018, according to new web application bug research released Wednesday.
Again these are vulnerabilities discovered, so the number of new plugins should not necessarily have any correlation and the increase in discoveries could be a good thing, but that isn’t ever grappled with or discussed in their post.