Fortinet’s FortiGuard Labs Is Putting Out Reports That Falsely Claim Vulnerabilities in WordPress Plugins Have Been Fixed
Recently if you were relying on other sources for information on vulnerabilities in WordPress plugins you use you would have seen it claimed that Envira Gallery Lite recently contained a vulnerability that was fixed in version 1.7.7.
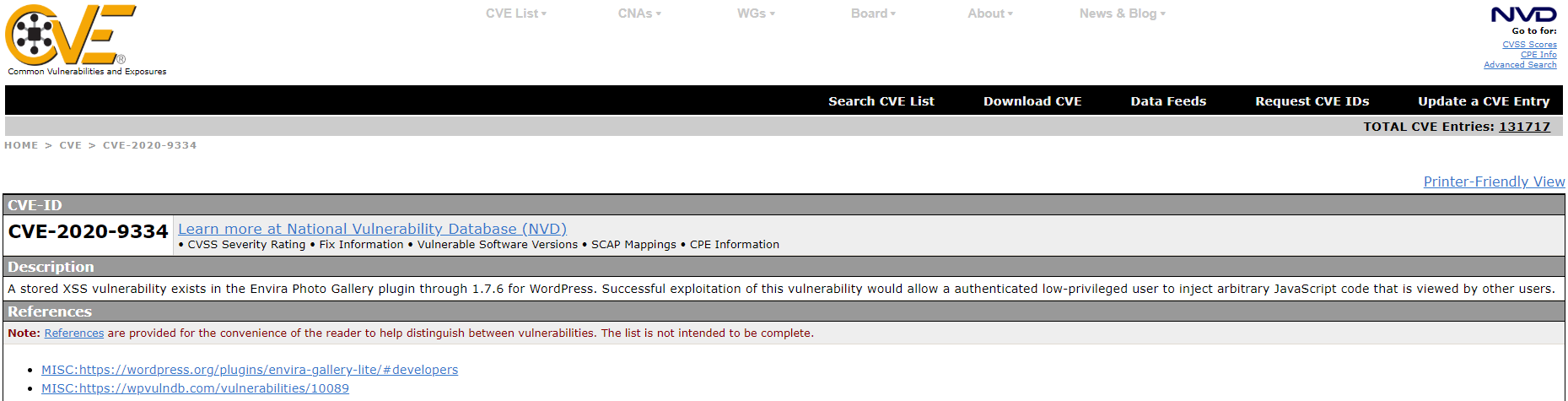
Here is that on the CVE :
Here is that on the WPScan Vulnerability Database:
If you look at the changes made in that version of the plugin though there simply couldn’t have been a security fix since no changes were made to the plugin’s code, other than to comments in it.
The changelog for that version doesn’t make any mention of a security update:
Updated: Minor code cleanup, updating authors.
When it comes to the WPScan Vulnerability Database that is yet another reminder of how low quality their data is and their lack of concern about spreading misinformation to their paying customers. But more important there is the question of if an unfixed vulnerability still exists in the plugin.
The original source of the claim there was a vulnerability and it was fixed in that version is Fortinet’s FortiGuard Labs. Just last week we noted how with another recent claim of a vulnerability from them the version claimed to fix the issue also didn’t include a security fix and there is still a vulnerability that matches most of what they described as the issue.
Fortinet didn’t provide much detail and some of it is clearly inaccurate, as they tell people to update to version 1.7.7:
Users should update the plugin to the latest version (1.7.7).
And they provide this timeline:
Fortinet reported the vulnerability to Envira Gallery Team on February 13, 2020
Envira Gallery Team confirmed the vulnerability on February 14, 2020
Envira Gallery Team patched the vulnerability on February 17, 2020
February 17 is when version 1.7.7 was released.
They neither provided any details on the code in question or a proof of concept, instead all that is included is this description:
A stored XSS vulnerability exists in the version of the plugin 1.7.6. Successful exploitation of this vulnerability would allow an authenticated low-privileged user to inject arbitrary javascript code into the plugin gallery image which is viewed by other users.
That is rather vague.
With one security provider that relies on the WPScan Vulnerability Database, wpsec.com, they put out a post that supposed to include a proof of concept for the vulnerability, though it involves an issue fixed over two years ago. In looking into that we realized there is in fact a vulnerability that seems to largely match the description that still exists in the plugin now.
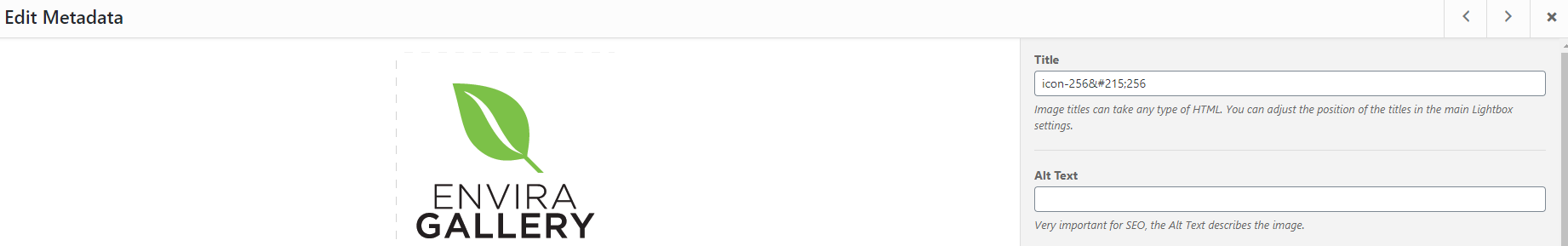
The plugin permits adding metadata for images in a gallery:
Under the Title entry is this text:
Image titles can take any type of HTML. You can adjust the position of the titles in the main Lightbox settings.
Unless users have the “unfiltered_html” capability they shouldn’t be allowed to use “any type of HTML”. The plugin though allows them to do just that and as the proof of concept below shows, leads to an unfixed authenticated persistent cross-site scripting (XSS) vulnerability.
WordPress Causes Full Disclosure
Due to the moderators of the WordPress Support Forum’s continued inappropriate behavior we changed from reasonably disclosing to full disclosing vulnerabilities in protest until WordPress gets that situation cleaned up, so we are releasing this post and then leaving a message about that for the developer through the WordPress Support Forum. You can notify the developer of this issue on the forum as well. Hopefully the moderators will finally see the light and clean up their act soon, so these full disclosures will no longer be needed (we hope they end soon). You would think they would have already done that, but considering that they believe that having plugins, which have millions installs, remain in the Plugin Directory despite them knowing they are vulnerable is “appropriate action”, something is very amiss with them (which is even more reason the moderation needs to be cleaned up).
Update: To clear up the confusion where developers claim we hadn’t tried to notify them through the Support Forum (while at the same time moderators are complaining about us doing just that), here is the message we left for this vulnerability:
Is It Fixed?
If you are reading this post down the road the best way to find out if this vulnerability or other WordPress plugin vulnerabilities in plugins you use have been fixed is to sign up for our service, since what we uniquely do when it comes to that type of data is to test to see if vulnerabilities have really been fixed. Relying on the developer’s information, can lead you astray, as we often find that they believe they have fixed vulnerabilities, but have failed to do that.
Proof of Concept
- Log in to WordPress as an Author-level user.
- Add a new gallery through /wp-admin/edit.php?post_type=envira.
- Add an image to the gallery.
- Click the Modify Image button on the image.
- Set the Title to
"><script>alert(document.cookie);</script>
- Click Save Metadata.
- Publish the gallery.
- Create a new post with the resulting gallery.
- When viewing the resulting post and clicking on the image an alert box with any available cookies will be shown.