WPScan and Patchstack Falsely Claim Vulnerability in WordPress Plugin with 20,000+ Installs Was Fixed
On May 31, 10 Web, the developer of the WordPress plugin Event Calendar WD, which has 20,000+ active installations according to wordpress.org, put out a new version of the plugin which has the changelog:
Fixed: XSS vulnerability.
The only other information available on that is the changes made in that version, 1.4.45 (it also includes the changes made in version 1.4.44). Our systems alerted us to that changelog entry and then we reviewed the changes being made. We couldn’t understand what the relevant change was actually supposed to do, so we tested things out found that the change made didn’t actually fix the security issue in the code and that the plugin was still vulnerable. The day after that version was released we provided details of what we found to our customers and started warning them if they were using the plugin. We also started trying to get together with the developer to get that fixed.
While we were able to get in touch with the 10 Web Security Team last week, that has still not led to a fixed version of the plugin being released and we are unaware of a timetable for that to happen.
For our customers, at least, they are aware of if they are impacted. For those relying on other data providers on vulnerabilities in WordPress plugins they have been told that a vulnerability was fixed in that version, despite that not being true and them using a plugin now known to be vulnerable.
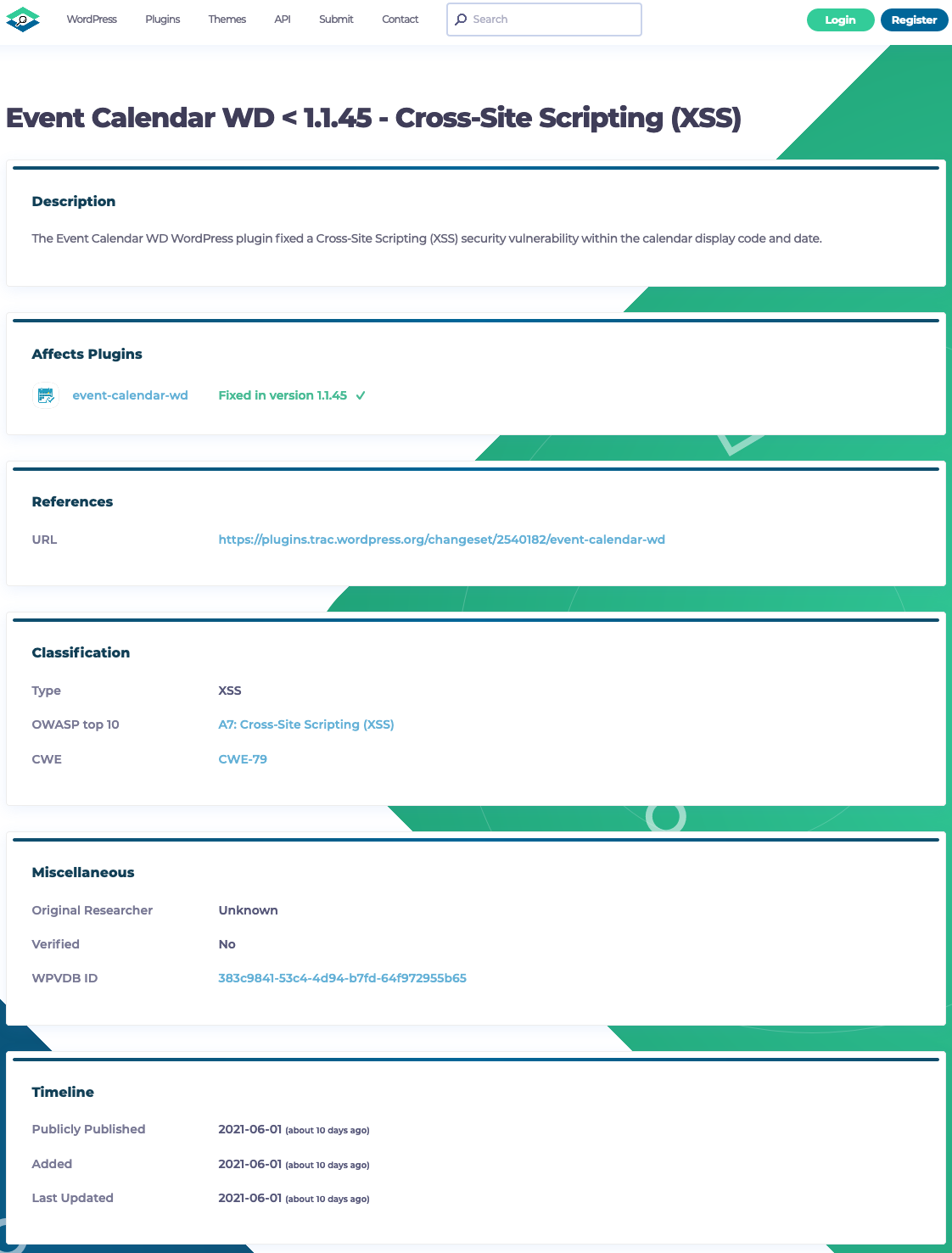
Here is WPScan’s listing (they also have confused a non-security fix done 1.4.44 with the attempted security fix):
You might have noticed that some how they are claiming this has been fixed, but also that it hasn’t been verified, which doesn’t make sense.
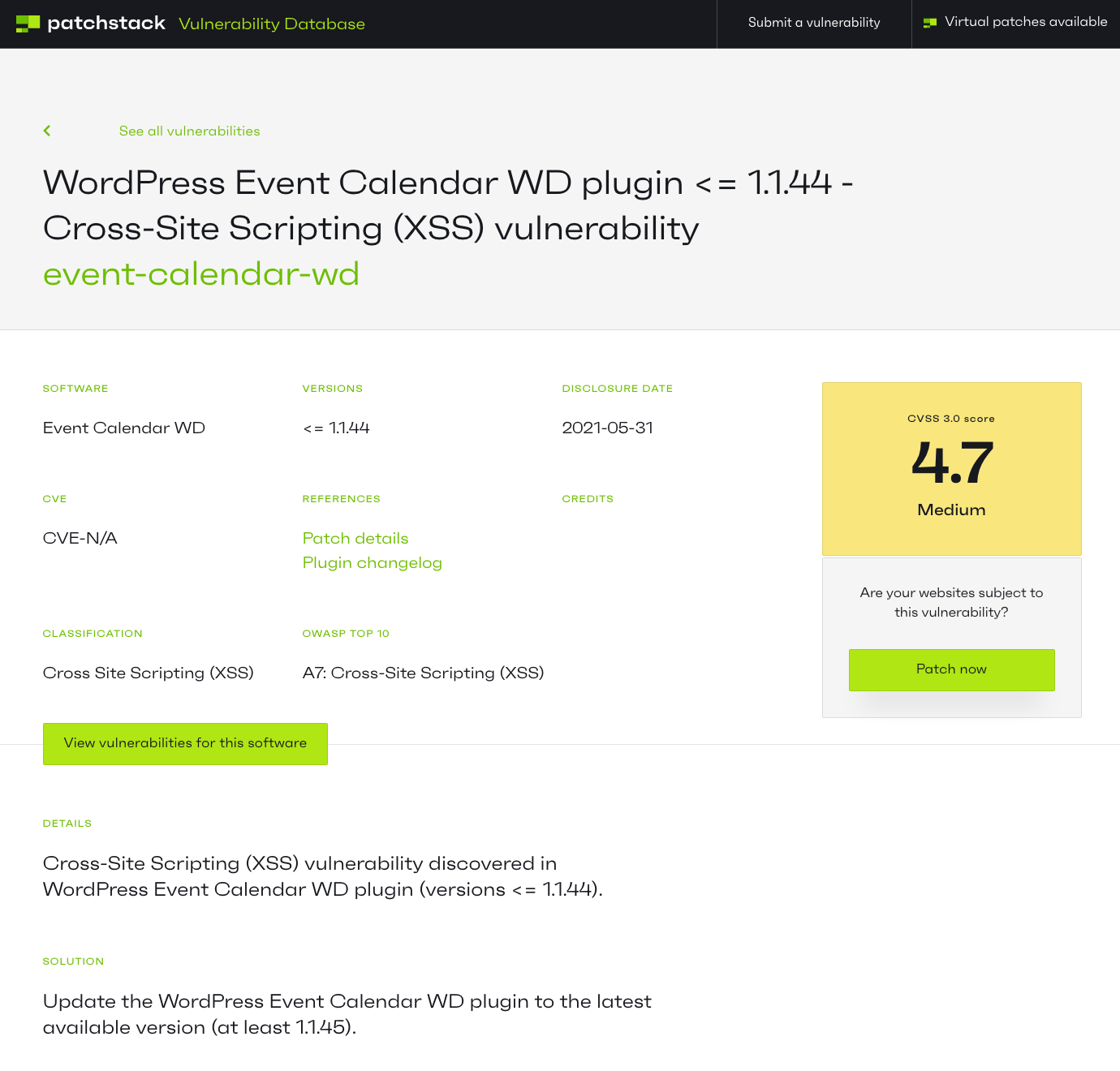
And here Patchstack:
They are claiming to provide a “virtual patch” for this, despite not even having done enough due diligence to realize the issue hasn’t been fixed.
Plugin Security Scorecard Grade for Patchstack
Checked on March 5, 2025See issues causing the plugin to get less than A+ grade