Web Host A2’s 50,000+ Install WordPress Plugin To Help Secure Websites Lacks Basic Security
A week ago we looked at a WordPress plugin promoting that it could improve the security of websites, while the plugin itself lacked basic security. It certainly isn’t alone in that. Take the web host A2’s A2 Optimized WP plugin, which is marketed as:
A2 Optimized is designed to make it quick and easy to speed up and secure your website by installing and configuring several well known, stable optimizations with a few quick clicks.
Code in the plugin got flagged by our proactive monitoring of changes made to plugins in the Plugin Directory to try to catch serious vulnerabilities. When we went manually check to see if there was a vulnerability, we found the code was not insecure in a way that would lead to a serious vulnerability, but missing security in that code, it turned out, is more broadly missing.
The plugin generally contains a lack of protection against cross-site request forgery (CSRF), which would allow an attacker to cause someone else to take an action they didn’t intend to.
That is easy to spot, so despite the plugin having 50,000+ installations according to wordpress.org, it would appear it hasn’t received a cursory security check, much less a more complete security review of the plugin. If A2 is interested in improving the security of WordPress websites, then getting a review of their plugin done would be a start. Recommending that plugins should have their security reviewed and or helping to make that happen, would be great.
Deleting a Plugin
Among the functionality in the plugin that isn’t properly protected, is the ability to delete a plugin installed on the website. So, for example, if you get someone logged in to WordPress as an Administrator to click on a link you control, you could have them visit the URL /wp-admin/admin.php?page=A2_Optimized_Plugin_admin&delete=Hello Dolly, which would cause the Helly Dolly plugin to be deleted.
The underlying code that leads to that starts with plugin’s registration of it admin page to accessible to user with manage_options capability, so Administrators:
559 560 561 562 563 564 565 566 567 | add_menu_page( $displayName, $displayName, 'manage_options', $this->getSettingsSlug(), array(&$this, 'settingsPage'), null, 3 ); |
After several steps, the function get_plugin_status() in the file /A2_Optimized_OptionsManager.php runs and the following code processes the deletion of a plugin:
1921 1922 1923 1924 1925 1926 1927 | if (isset($_GET['delete'])) { foreach ($this->plugin_list as $file => $plugin) { if ($_GET['delete'] == $plugin['Name']) { $this->uninstall_plugin($file); } } } |
That code and the code that runs before lacks a nonce check to prevent CSRF. That is also true of the function it calls to handle the deletion, uninstall_plugin();
2050 2051 2052 2053 2054 2055 2056 2057 2058 2059 2060 2061 | public function uninstall_plugin($file, $delete = true) { require_once ABSPATH . 'wp-admin/includes/plugin.php'; require_once ABSPATH . 'wp-admin/includes/plugin-install.php'; $this->deactivate_plugin($file); uninstall_plugin($file); if ($delete) { delete_plugins(array($file)); } unset($this->plugin_list[$file]); $this->clear_w3_total_cache(); } |
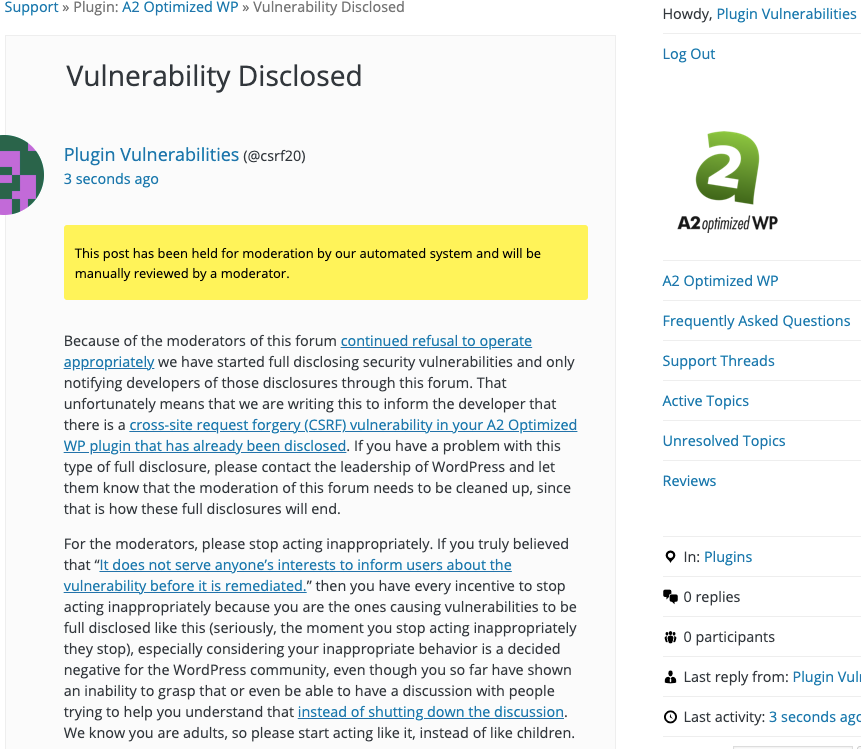
WordPress Causes Full Disclosure
Because of the moderators of the WordPress Support Forum’s continued inappropriate behavior we changed from reasonably disclosing to full disclosing vulnerabilities for plugins in the WordPress Plugin Directory in protest, until WordPress gets that situation cleaned up, so we are releasing this post and then leaving a message about that for the developer through the WordPress Support Forum. (For plugins that are also in the ClassicPress Plugin Directory, we will follow our reasonable disclosure policy.) You can notify the developer of this issue on the forum as well. Hopefully, the moderators will finally see the light and clean up their act soon, so these full disclosures will no longer be needed (we hope they end soon). You would think they would have already done that, but considering that they believe that having plugins, which have millions installs, remain in the Plugin Directory despite them knowing they are vulnerable is “appropriate action”, something is very amiss with them (which is even more reason the moderation needs to be cleaned up).
Update: To clear up the confusion where developers claim we hadn’t tried to notify them through the Support Forum (while at the same time moderators are complaining about us doing just that), here is the message we left for this vulnerability:
Is It Fixed?
If you are reading this post down the road the best way to find out if this vulnerability or other WordPress plugin vulnerabilities in plugins you use have been fixed is to sign up for our service, since what we uniquely do when it comes to that type of data is to test to see if vulnerabilities have really been fixed. Relying on the developer’s information can lead you astray, as we often find that they believe they have fixed vulnerabilities, but have failed to do that.
Proof of Concept
The following proof of concept will delete the plugin Hello Dolly, when logged in as an Administrator.
Replace “[path to WordPress]” with the location of WordPress.
http://[path to WordPress]/wp-admin/admin.php?page=A2_Optimized_Plugin_admin&delete=Hello Dolly