Authenticated PHP Object Injection Vulnerability in Aarambha Kits for Elementor
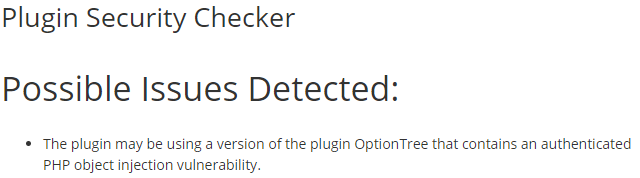
One way we help to improve the security of WordPress plugins, not just for customers of our service, but for everyone using them, is our proactive monitoring of changes made to plugins in the Plugin Directory to try to catch serious vulnerabilities. Through that, we caught a variant of one of those vulnerabilities, an authenticated PHP object injection vulnerability in a brand new plugin, Aarambha Kits for Elementor.
We now are also running all the plugins used by our customers through the same system used for the proactive monitoring on a weekly basis to provide additional protection for them. [Read more]