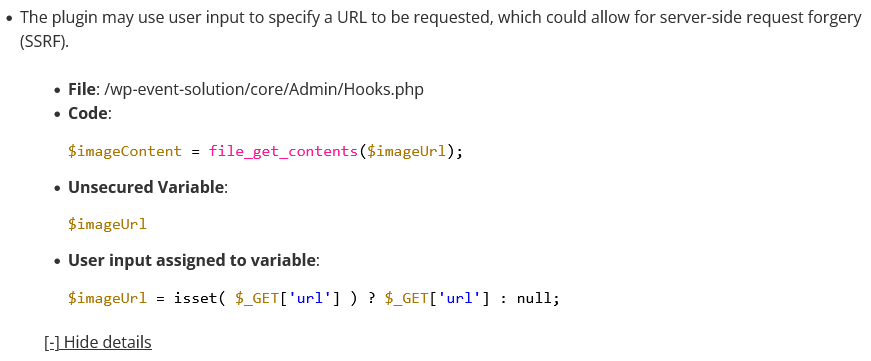
Last week two of the 1,000 most popular WordPress plugins were closed and we found that both of those contained security vulnerabilities that seemed unrelated to the closure. That doesn’t seem to paint a great picture as to the security of WordPress plugins or for the concern for security by the people running the WordPress Plugin Directory. It’s now a new week and the story continues. Earlier today another one of the 1,000 most popular plugins, Essential Addons for Elementor, which has 100,000+ installs was closed. Since then a couple of updates have been made to the plugin, which may or may not be related to the closure. We didn’t see any obvious security changes in those updates, so we went to check to see if there were any obvious security issues that remain in the latest version, since we are interested in warning our customers if they are using vulnerable plugins. A few checks in, we found multiple security issues with the plugin, for now we will detail an authenticated server-side request forgery (SSRF) vulnerability, which can also be exploited through cross-site request forgery (CSRF).
If the developer or someone else wants the plugin more fully review for security, we offer security reviews for a fee (and also allow customers of our main service to suggest/vote for plugins to get a review from us for no additional fee). [Read more]