Responsible Disclosure and Closing a WordPress Plugin With an Unfixed Vulnerability Didn’t Prevent Websites From Being Hacked
One of the things we do to keep track of vulnerabilities in WordPress plugins to warn customers of our service if they are using publicly known insecure plugins is monitoring WordPress support forum. Recently that hasn’t led to us finding out about any vulnerabilities we didn’t know about, but it does provide a regular reminder of the lack of concern of people in charge of WordPress about addressing the poor handling of security problems with plugins.
Yesterday a topic was started on the forum of Rich Reviews, “Plugin not supported; open to malware – uninstall now!“, which starts:
Since this plugin is no longer on the repository or supported, it is highly suggested to remove this plugin. 3 of 4 of my sites using it were affected by the script malware
If you go to main page for the plugin on the Plugin Directory there is this warning:
This plugin has been closed as of March 11, 2019 and is not available for download. Reason: Security Issue.
While that warning is there, no warning is provided to those already using the plugin and based on the replies the original poster isn’t the only one still using the plugin.
The current amount of installs of the plugin isn’t listed due to the plugin being closed, but on January 9 there were 10,000+ installs, so somewhere between 10,000 and 20,000 installs.
That so many people were using that plugin at that time is itself a bad sign as the vulnerability being exploited now sounds like it could one that we had disclosed in December of 2017. We had notified the developer of that vulnerability over a month and half before disclosure, along with two lesser issues. While the lesser issues were resolved before our disclosure, the more serious issue was not and still hasn’t been.
Plenty of Room for Improvement
There is a lot that could have been done differently here and WordPress could easily improve their processes going forward, but based on the years long track record of inaction it seems unlikely that will happen, but everyone can hope.
Why did the plugin remain in the Plugin Directory for over a year after we had warned about the vulnerability? The simple answer is that we appear to have been the only ones that ever tried to make sure that publicly known vulnerable plugins were not remaining in the Plugin Directory. When we suspended doing that in June of 2017 due to continued poor handling of security by the WordPress team, they didn’t pick up the slack, so you now have plugins with millions of installs that are known to be vulnerable still in that.
Years ago, shortly after we had started notifying the team running the Plugin Directory about those unfixed vulnerabilities, we realized the problem with people already using plugin being left unaware that they were using plugins that were closed on the Plugin Directory. We had then suggested on the Ideas section of the WordPress to start alerting people, while that was the marked as ‘Good idea! We’re working on it”, since then the people on the WordPress side of things have given a litany of strange excuses for not doing that. Here for example is the head of the team running the Plugin Directory claiming that not warning about an unfixed vulnerability is the proper response when a vulnerability is already being exploited:
We cannot provide this service at this time.
IF an exploit exists and we publicize that fact without a patch, we put you MORE at risk.
If an exploit exists, hackers will be targeting the vulnerability en-mass.
That’s exactly the issue. If we make it known there is an exploit, the hackers attack everyone :/
If we don’t tell anyone, then hackers who DO know will attack, but they would have anyway.
You don’t have to be a security expert to realize that leaving people to be hacked isn’t a proper resolution for that. There is another option, as mentioned on the security page on the WordPress website:
When a plugin vulnerability is discovered by the WordPress Security Team, they contact the plugin author and work together to fix and release a secure version of the plugin. If there is a lack of response from the plugin author or if the vulnerability is severe, the plugin/theme is pulled from the public directory, and in some cases, fixed and updated directly by the Security Team.
Despite our repeated offer to provide the fixes, so the team wouldn’t have to do almost any work, we can’t even recall the last time that option was used with a vulnerability that is being exploited. We tried to discuss the lack of doing that in the past and they have refused to even discuss the lack of doing that. In one instance we tried to do that involved an unfixed vulnerability in the plugin Form Lightbox that appears to have originally been exploited in July of 2016 and was recently claimed by Wordfence to still being exploited.
Protecting Yourself
We continue to be willing to work the WordPress team to resolve these problems, but since that isn’t happening our service can fill the gap. If you used our service and this plugin you would have been warned it was vulnerable back in 2017 or whenever you first set up the service.
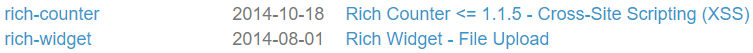
Relying on other data sources likely wouldn’t have done that, as underlying source of most of those is the WPScan Vulnerability Database and that doesn’t include the vulnerability in its data set: